Finding Hidden Wireless Networks
Blogs: Security
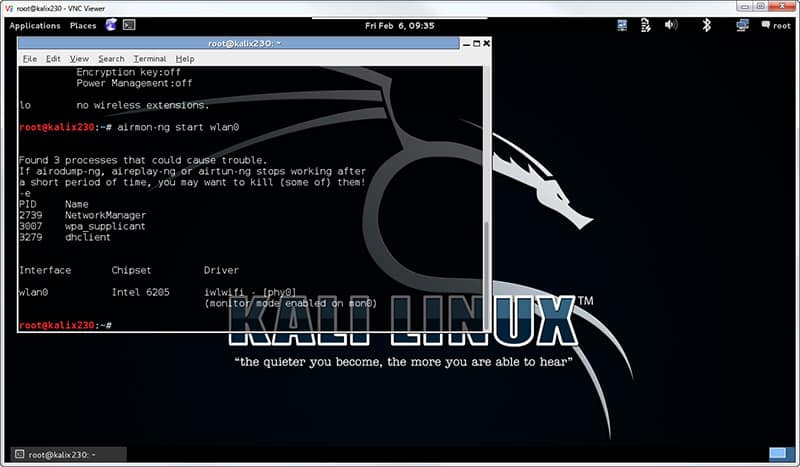
Finding Hidden Wireless Networks
0 3Many Wi-Fi network administrators decide to disable SSID broadcasts. They do this, in part, in an attempt to hide their network from uninvited users. The common belief behind it is that if the network name is not being broadcast, it is harder for an attacker to find the network. Nothing could be farther from the … Continue reading Finding Hidden Wireless Networks
The Best Anti-Phishing Tool in the Enterprise… Is Free!
0 0Phishing is a combination of social engineering and technology that tries to trick users into disclosing sensitive information. You’re probably already familiar with the stereotypical Nigerian Prince email – an unsolicited email from an unknown sender identifying himself as a Nigerian Prince and offering to pay you to help him transfer his money to your … Continue reading The Best Anti-Phishing Tool in the Enterprise… Is Free!
Security+ SY0-301 versus SY0-401 and other questions
1 0The SY0-401Security+ exam went live in April 2014, though you may still take the SYO-301 exam through December 31, 2014. In either event, the Security+ credential is now a Continuing Education certification such that you will want to update your knowledge and skill sets regardless of the exam version you initially pass. While teaching our … Continue reading Security+ SY0-301 versus SY0-401 and other questions
Using Nmap to Reconnoiter the DMZ and Perimeter Networks
0 1The importance of reconnaissance in vulnerability discovery and penetration testing is usually overlooked. Network security personnel with little training or experience will often begin their analysis by finding a few target systems and immediately attempt to compromise their security with user/password logins and vulnerability penetration tests. These premature attempts to compromise pseudo-random hosts are likely … Continue reading Using Nmap to Reconnoiter the DMZ and Perimeter Networks
Using WebRipper to Examine Website Content
0 0A skilled attacker usually begins an attack by performing detailed reconnaissance. Recon is critical to a comprehensive attack as it yields information about the target network, hosts, personnel, publicly accessible assets, and a host of other data. One of the easiest targets is a website. Websites are, by design, highly accessible and loaded with data. … Continue reading Using WebRipper to Examine Website Content
Using SuperScan to Reconnoiter an Internal Network
0 0The importance of reconnaissance in vulnerability discovery and penetration testing is usually overlooked. Network security personnel with little training or experience will often begin their analysis by finding a few target systems and immediately attempt to compromise their security with user/password logins and vulnerability penetration tests. These premature attempts to compromise pseudo-random hosts are likely … Continue reading Using SuperScan to Reconnoiter an Internal Network
A Malware Recovery Scenario – Hacktool
0 0A former student sent me an email requesting assistance with a computer issue. Microsoft Security Essentials continued to post the message “error warning: HACKTOOL:WIN32/Keygen”. Hacktool malware was quarantined. Other symptoms started to appear. Following appropriate guidance, the student looked into the event viewer. The most often repeated error that the student noticed was “The driver … Continue reading A Malware Recovery Scenario – Hacktool
Project Management (PMP) for Executives – Introduction
1 96 0Introduction Project Management (PMP) for Executives is a 9 part video training series developed by Steve Fullmer, PMP, MBA, MCT/CTT+, CDP. Steven has a global reputation as a project manager, chief technology officer, and computer systems innovator. He has authored more than 100 articles and a dozen courses in the fields of project management, productivity, business … Continue reading Project Management (PMP) for Executives – Introduction
Project Management (PMP) Leadership Skills in the 21st Century … Do you Know Your History? – November 10, 2017
0 99 2The PMI Leadership triangle touts our need to develop our knowledge and application of leadership. Do you understand the leadership models of the 20th century? The 21st Century? Understanding your predecessors can assist to set your future course. On the matter of history, Mark Twain’s quote “History doesn’t repeat itself, but it does rhyme” is … Continue reading Project Management (PMP) Leadership Skills in the 21st Century … Do you Know Your History? – November 10, 2017
Principles of Decision Tree Design and Analysis in Project Management (PMP)
0 59 0In this Project Management Professional (PMP) training video, learn how about Decision Trees and how to solve them with Risk Analysis. Existentialism conveys themes like the importance of choice, contingencies, and extreme situations. How do you choose when the decision is hard? (If the decision is easy, you just choose.) When the decision is hard, we … Continue reading Principles of Decision Tree Design and Analysis in Project Management (PMP)
Understand the Mind to Become a Better Project Manager – February 18, 2015
0 98 2Our minds all work alike, at least biologically. Yet we are a diverse species with different motivations, opinions, perspectives, and directions. Do you understand how and why the human mind works? What makes you a great project manager? In this recording of our PMP training webinar from February 18, 2015, Steve Fullmer covers some of … Continue reading Understand the Mind to Become a Better Project Manager – February 18, 2015
Windows 10 Security – What’s New and Improved? – December 3, 2015
0 104 1In this recording of our Windows 10 webinar from December 3, 2015 training, security expert Mike Danseglio presents the enhanced security features of SmartScreen, Defender and BitLocker in Windows 10 and new features such as Biometric Identification, Microsoft Passport, Device Guard and more.
Windows 10 Managing, Deploying and Configuring – December 2, 2015
0 486 1In this recorded Windows 10 training webinar from December 2, 2015, Windows Server instructor Rick Trader presents the deployment and management of Windows 10 Enterprise and the new Provisioning capability in Windows 10. Learn how to manage Windows 10 deployments using System Center Configuration Manager, Mobile Device Management and Intune. Also included in his presentation … Continue reading Windows 10 Managing, Deploying and Configuring – December 2, 2015
Project Management (PMP) for Executives – Introduction
1 96 0Introduction Project Management (PMP) for Executives is a 9 part video training series developed by Steve Fullmer, PMP, MBA, MCT/CTT+, CDP. Steven has a global reputation as a project manager, chief technology officer, and computer systems innovator. He has authored more than 100 articles and a dozen courses in the fields of project management, productivity, business … Continue reading Project Management (PMP) for Executives – Introduction
Project Management (PMP) Leadership Skills in the 21st Century … Do you Know Your History? – November 10, 2017
0 99 2The PMI Leadership triangle touts our need to develop our knowledge and application of leadership. Do you understand the leadership models of the 20th century? The 21st Century? Understanding your predecessors can assist to set your future course. On the matter of history, Mark Twain’s quote “History doesn’t repeat itself, but it does rhyme” is … Continue reading Project Management (PMP) Leadership Skills in the 21st Century … Do you Know Your History? – November 10, 2017
Principles of Decision Tree Design and Analysis in Project Management (PMP)
0 59 0In this Project Management Professional (PMP) training video, learn how about Decision Trees and how to solve them with Risk Analysis. Existentialism conveys themes like the importance of choice, contingencies, and extreme situations. How do you choose when the decision is hard? (If the decision is easy, you just choose.) When the decision is hard, we … Continue reading Principles of Decision Tree Design and Analysis in Project Management (PMP)
Understand the Mind to Become a Better Project Manager – February 18, 2015
0 98 2Our minds all work alike, at least biologically. Yet we are a diverse species with different motivations, opinions, perspectives, and directions. Do you understand how and why the human mind works? What makes you a great project manager? In this recording of our PMP training webinar from February 18, 2015, Steve Fullmer covers some of … Continue reading Understand the Mind to Become a Better Project Manager – February 18, 2015
Windows 10 Security – What’s New and Improved? – December 3, 2015
0 104 1In this recording of our Windows 10 webinar from December 3, 2015 training, security expert Mike Danseglio presents the enhanced security features of SmartScreen, Defender and BitLocker in Windows 10 and new features such as Biometric Identification, Microsoft Passport, Device Guard and more.
Windows 10 Managing, Deploying and Configuring – December 2, 2015
0 486 1In this recorded Windows 10 training webinar from December 2, 2015, Windows Server instructor Rick Trader presents the deployment and management of Windows 10 Enterprise and the new Provisioning capability in Windows 10. Learn how to manage Windows 10 deployments using System Center Configuration Manager, Mobile Device Management and Intune. Also included in his presentation … Continue reading Windows 10 Managing, Deploying and Configuring – December 2, 2015
A Simple Introduction to Cisco CML2
0 3894 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 642 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 725 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments