A quick look at Cisco Modeling Labs (CML)
A quick look at Cisco Modeling Labs (CML)
When I attended Cisco Live 2015 in San Diego earlier this year, one of the sessions presented was about Cisco Modeling Labs (CML). This is a Cisco product which allows a user to virtualize a company’s network environment. I have previously blogged about VIRL, which is, in essence, an individual user version of the product, while CML is for enterprise-level virtualization needs. The presenter, Craig Brown, did an excellent job of demonstrating CML, and I was fortunate enough to receive a 30-day license to the product. I wanted to share some screenshots which show the user’s view of this product. Let’s take a look.
The install of the product occupied much of a Sunday while I was gathering all the necessary pieces to make it go. Now that I have completed all the steps, I will list them here so you can see what is involved in accessing this environment. Launch VMWare Workstation (not free), launch ESXi (free), launch VMWareVSphere Client (nowhere near free, but since I had a time bombed license to CML, I downloaded an eval of VSphere), use the VSphere client to launch the CML Virtual Machine (downloaded from Cisco as part of the 30-day license), and the behind-the-scenes stuff is ready. Now launch the CML client (also available from Cisco) to access the environment. [Note: There is a 32-bit version and a 64-bit version of the client, but I could only get the 32-bit version to function correctly on my 64-bit machine. Not sure why there was an issue with the 64-bit version, but I did send a note off to Craig to let him know.] Figure 1 shows how the icon for this UI client looks on my desktop:
Figure 1
Now to launch it!
Figure 2
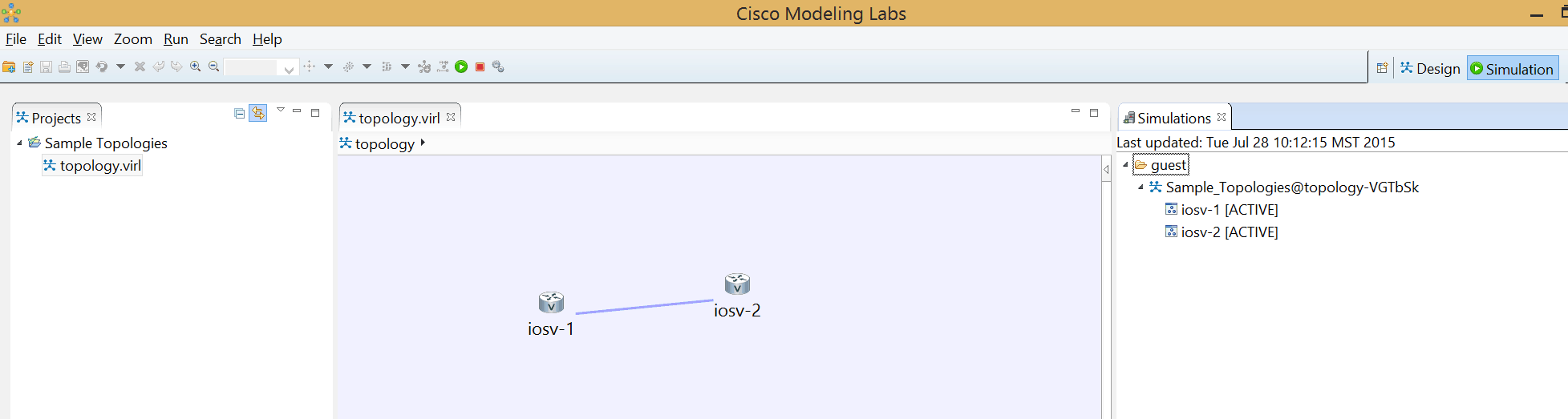
Take a look at that! It looks nothing like VIRL. Oh wait, it looks just like VIRL. If you read Cisco’s description of the two products, you will of course note that the CML product is far more scalable and is fit for modeling a network to as large as you need. (By the phrase, “as large as you need,” I mean for as large as you can afford to purchase node licensing. CML, like VIRL, is subscription-based, and the more you spend, the more nodes you can have.) For the little guy, the initial install of the product with the default number of nodes, which is 15, reveals two products that look remarkably similar
You can see from figure 2 that I have already created a simple topology, a process which is identical to the way topologies are created in VIRL. So let’s log in to my two devices. I use SecureCRT to access my devices as opposed to using the included console access method, because I like the freedom and the familiarity that goes with a product I have used for a long time. You can use any terminal emulator you wish, or just use the included console access. I have configured EIGRP as a routing protocol, and the two routers see each other as CDP neighbors. Let’s observe the resulting routing table from iosv-1, shown in figure 3:
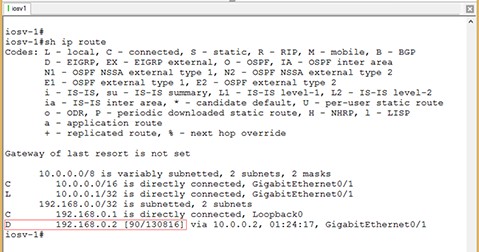
Figure 3
So EIGRP is running, and I even have an EIGRP-learned route in my table, as indicated by the ‘D.’ So far, it seems to perform just like VIRL. Let’s add named EIGRP configuration to our scenario.
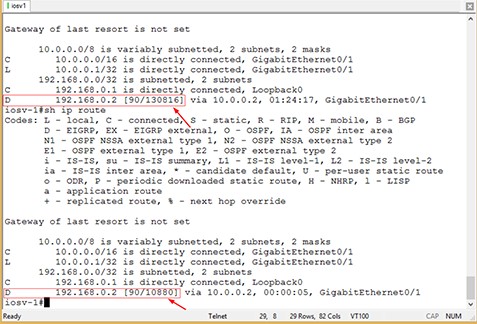
Figure 4
Note that figure 4 is unchanged (at the top portion of the screenshot) from figure 3. That’s because I didn’t clear the screen, but left the output available for comparison. Once I configured named-mode EIGRP and those processes neighbored up, the routing table of iosv-1 changed. As mentioned in my previous blog, the metric calculation for named-mode is a bit different, even though the DUAL (Diffusing Update Algorithm) is still used. This being the case, the route with the better metric is installed in the routing table, and it is the one learned from the named-mode process. How can we tell? Let’s look at the details of the route:
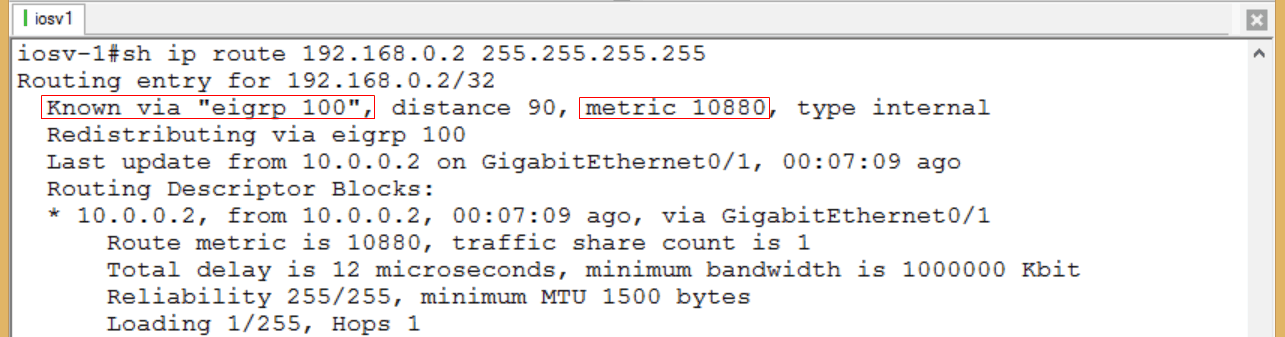
Figure 5
The configuration in my little topology has ‘classic’ EIGRP running with AS number 1, and named-mode running with number 100. So it is clear from figure 5 that the named-mode route is installed in the routing table.
The purpose of this blog is not to go into the details of configuring EIGRP, but to show the similarities between CML and VIRL. If you look at my previous named-mode EIGRP blog and this blog side-by-side, they look similar. At the entry level, the products will appear and function almost identically. You don’t begin to see a difference until you start building out massive network topologies, of which CML is capable. From an enterprise network perspective, it is of great value to be able to model your existing or proposed topology and test out the bugs before deploying into a production environment.
Interesting to note that while I was prepping this blog for posting, I once again conversed with Craig regarding CML and he provided me with some additional technical gems about the product: “’Unlimited scaling’ also means based on hardware (as well as license). The general rule of thumb is that you can get 3 virtual nodes to 1 core processor. This was tested using IOSv and OSPF network, but your mileage will vary depending on the type of processor being used (some old server you found in the shed vs latest UCS) and also on the routing protocols, traffic, etc. It all comes down to how much load is being put into the computer. The way around this to scale is to load onto another server, or blade, another virtual network and connect them via external connection. We are researching how to run 1000s of nodes on a single server, but that’s a work in progress with no timeframes yet.”
He also had a suggestion on how to reduce the out-of-pocket expenses if you are ‘the little guy,’ as he mentioned that CML also works with VMWare Player, which is free.
If you are seriously considering how much CML bang you can get with your existing (or pending) hardware buck, Craig shared a CML Calculator that anyone can use to run the memory/proc/node computations.
So if you are a recommender for your company’s network team, get to the next budget meeting and make them aware of the CML solution. Either that, or buy a second copy of everything in your production network to build a test network. Hmmm…which option has more ROI?
I had to type fast to complete this blog – my license expires in 3 days!
If you have questions or comments, please feel free to post them!
Until next time…
Mark Jacob
Cisco and CompTIA Network + Instructor – Interface Technical Training
Phoenix, AZ
You May Also Like
Cisco Modeling Labs, CML, CML Calculator, VIRL, virtualization, VMWare workstation, VSphere Client
A Simple Introduction to Cisco CML2
0 3901 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 643 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 731 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments