Accessing Advanced Wireless Settings for Intel Wireless Adapters
Accessing Advanced Wireless Settings for Intel Wireless Adapters
“Does it matter which wireless adapter is in my new laptop?”
I get this question whenever a coworker or friend is buying a new laptop. My first answer is that it depends on what they want to do with it. For basic users, no, it usually doesn’t matter. Any old wireless network adapter (WNIC) will provide the same level of functionality – from their perspective.
Administrators and IT security staff usually want to do more with their WNIC. I always advise those people to buy a laptop with an Intel WNIC.
Firstly, the Intel design and build quality are superb. They are miracles of tiny performance. For example, here are a couple of photos of a brand-new Intel 7260 dual-band 802.11ac adapter that I received today. I added a US dime in these photos for scale reference.
Figure 1. Front of the Intel 7260 dual-band AC adapter.
Figure 2. Rear of the Intel 7260 dual-band AC adapter.
Do you see what I mean? The design is clean, yet this sucker is powerful. However, the power is only really unlocked when you install the Intel PROSet drivers.
Basic Wireless Adapter Drivers Are Limited
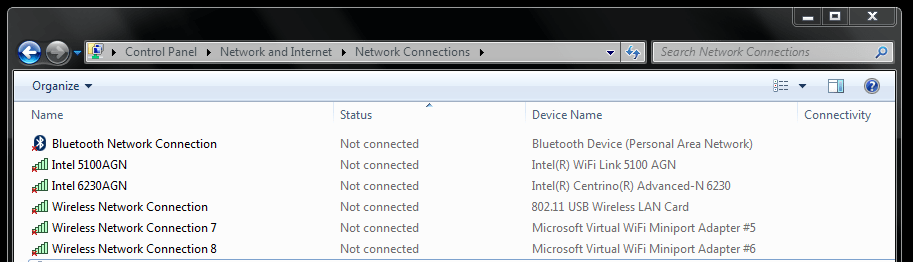
Windows drivers are able to expose increased device capabilities. This is especially true in the WNIC category. As an example, I have a Lenovo laptop configured with several WNICs as shown in Figure 3.
Figure 3. Two Intel WNICs and one run-of-the-mill WNIC.
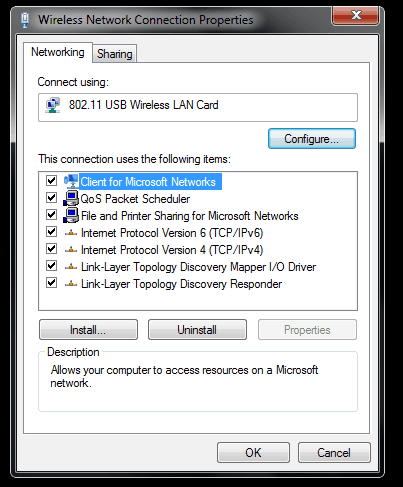
First I’ll show you the very basic WNIC settings for the 802.11 USB Wireless LAN Card device. I just right-click on the adapter and choose Properties to bring up the connection properties dialog.
Figure 4. The Wireless Network Connection Properties of the boring WNIC.
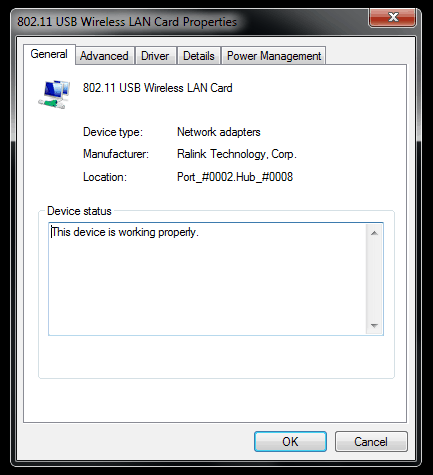
Now I click Configure, and as you can see in Figure 5 this is a RAlink USB adapter.
Figure 5. The Ralink Technology adapter properties.
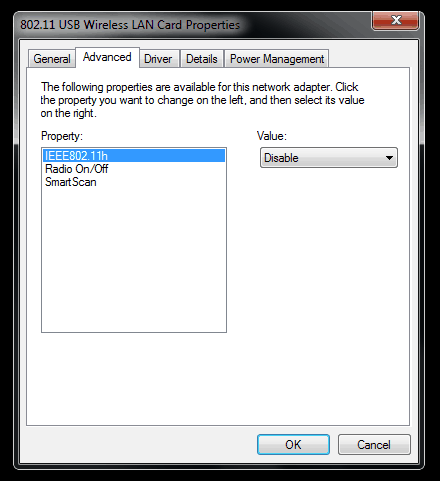
Clicking the Advanced tab shows me the sparse configuration options available for this adapter.
Figure 6. So very few options…
There’s not much to optimize or configure here. Now compare that with…
Intel PROSet Wireless Drivers Are Awesome
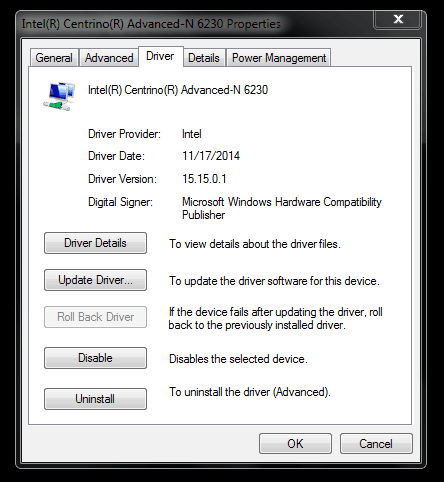
I’ve already installed the Intel PROSet Wireless drivers from the Intel Download Center. Now when I bring up the properties and show the Driver tab as shown in Figure 7 I can see that these are Intel drivers, not Windows inbox drivers.
Figure 7. Verifying the Intel drivers are in use for the Intel Centrino Advanced-N 6230.
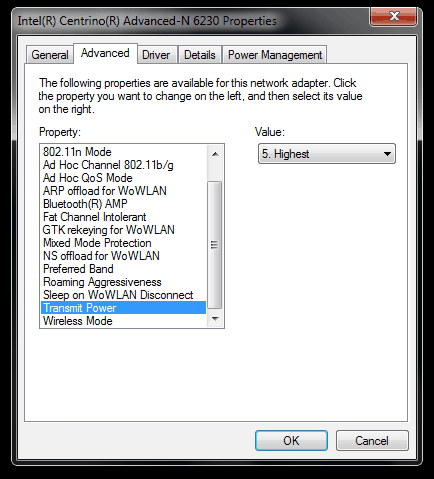
Finally I can bring up the Advanced settings tab as shown in Figure 8.
Figure 8. A hardware hacker’s dream come true.
Amazing! I can now adjust just about any capability and setting on this Intel WNIC. These settings are retained across system restarts, so once I optimize the configuration I’m not required to do it again.
Enjoy!
Mike Danseglio -CISSP / MCSE / CEH
Interface Technical Training – Technical Director and Instructor
Mike Danseglio teaches Security classes at Interface Technical Training. His classes can be attended in Phoenix, Arizona or online from anywhere in the world with RemoteLive.
- CISSP (Certified Information Systems Security Professional)
- Certified Ethical Hacking and Countermeasures v8
- Computer Hacking Forensic Investigator – CHFI v8
- CompTIA Security + Certification Skills
You May Also Like
A Simple Introduction to Cisco CML2
0 3901 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 645 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 731 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments






See what people are saying...