How to get more comfortable with IPv6
How to get more comfortable with IPv6
If you are new to the world of networking, perhaps considering putting in the effort to achieve Network + certification, you may wish you were more comfortable with IPv6. If you are already an IPv6 guru, this may be child’s play for you. Yet it turns out that if you are already comfortable with IPv4, you are not far away from treating IPv6 like an old friend. I like to make comparisons between IPv4 and IPv6 to make the connections easier. Most of the reluctance to ‘liking’ IPv6 seems to be due to unfamiliarity. Let’s dispel some of that unfamiliarity right now.
Let’s take something we already know and use it as leverage to learn more. Consider a Class B network in IPv4. For example, 172.16.0.0 255.255.0.0. Using CIDR notation, this can also be written as 172.16.0.0 /16, pronounced ‘slash sixteen.’ We know that in IPv4, this means that the first sixteen bits ‘belong’ to the network, or identify network bits. The easy way to keep this straight is to imagine that these bits are now chiseled in granite, or that they cannot move. Figure 1 shows how this looks in binary:
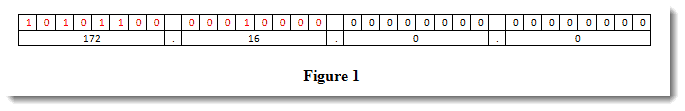
The red bits in Figure 1 are the ones that can’t move. The black bits are free to move about. This may seem elementary, but the concept applies in IPv6 as well. The official dirt on IPv6 is contained in RFC 4291. I want to take one small snippet from that RFC and build on it here, using the above information as a base. Figure 2 shows section 2.4 of RFC 4291:
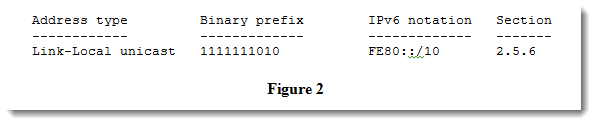
You may know that IPv6 has 128 bits, as opposed to the 32 bits in IPv4. IPv4 is usually written using dotted-decimal notation, for human consumption. IPv6 is written in hexadecimal, which may make it seem un-human-friendly. It turns out, that is far from the truth. Consider writing IPv6 in dotted-decimal like IPv4, what would that look like? Let’s say we break a full IPv6 address into octets (chunks of 8 bits). Instead of four octets as in IPv4, it would take 16 octets to write an uncompressed IPv6 address. No wonder they don’t do it that way. Now back to the main topic, what does the slash notation mean in IPv6?
Figure 2 shows the link-local IPv6 address, which ends with /10. No need to scrap any prior knowledge here – /10 means what we think it means – that the first ten bits ‘belong’ to, or identify, the network. Figure 3 shows an IPv6 chart similar to the IPv4 chart shown in Figure 2.
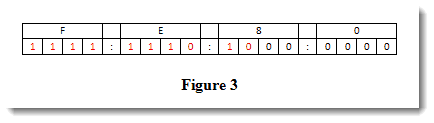
Once again, the red bits indicate bits that will not move. The black zeroes are free to change. This means that, much like a route summarization in IPv4, the notation FE80::/10 indicates a block of network information. We can expand on the table in Figure 3 to see how far this block extends in the third hexadecimal quartet. This is shown in Figure 4:
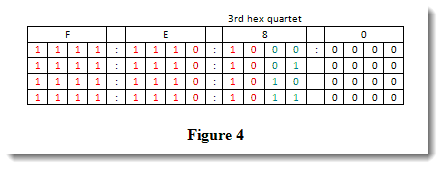
Like before, the red bits don’t move. But keep an eye on the third hexadecimal quartet and the green bits. You can see how they roll through all their possible combinations from zero to three. However, behind the scenes, even though I am writing a (portion of) 128 bit address in binary, it is normally written in hex. So let’s interpret that third section in hex:
Binary Hexadecimal
1000 8
1001 9
1010 A
1011 B
This means valid link-local addresses can be represented as FE80, FE90, FEA0, and FEB0. That being said, I have not encountered in the wild any link-local address representation other than the typical FE80 variety. Maybe that’s because there are so many valid link local addresses that begin with FE80, there is no need to use the rest. Maybe someday in a galaxy far far away.
If you have any thoughts on your experiences with IPv6, I would love to hear them…
This is an example of what you will learn in the CompTIA Network + Certification class at Interface Technical Training.
For instructor-led CompTIA Certification classes, see our course schedule.
Until next time.
Mark Jacob
Cisco and CompTIA Network + Instructor – Interface Technical Training
Phoenix, AZ
You May Also Like
CIDR notation, Class Inter Domain Routing, dotted-decimal, FE80, hexadecimal, IPv6, link-local, slash notation
A Simple Introduction to Cisco CML2
0 3901 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 643 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 731 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments