How to Recover Locked Windows 7 Files
How to Recover Locked Windows 7 Files
One of my Windows 7 students shared a scenario that has several possible root causes, and therefore several possible repairs.
The scenario: a program and file in use are closed. Attempts to move the file indicate that the file is still open and Windows will not allow a move or rename of the file.
Microsoft provides only modest directions for identifying and recovering locked files. Why can’t I delete a file or folder?
Although the specific program was not identified, one of the more common issues associated with Microsoft Office applications, amongst others, is the creation of temporary files that may remain if the application terminates improperly. For instance, it is always best to use the File-Close or Quit Application menu options rather than just resorting to program termination using the red “X” on the application window.
Graham Mayor provides a thorough overview for resolving file locks when Word 2002, 2007 or 2010 terminates improperly. What to do when Word crashes? The key in this instance is to locate the system temporary folder (identified by %temp%) and to remove all the associated temporary files that may result in a file lock scenario. Do not just look for folders named ‘temp’ or you may not locate the files you seek.
Using Restore Points to Recover a File
Before resorting to any manual file removal or cleanup, I strongly recommend creating a system backup or using the Windows 7 System Protection option to create a Restore Point. Type “Restore Point” in the Start search box and select ‘Create a Restore point’. The System Properties > System Protection panel will launch.
Prior to file deletion, Configure System Protection. You want to select Restore System Settings and Previous Versions of Files as seen below. Then Create a Restore Point. If you accidentally delete an important file, you now have a simple means to restore it.
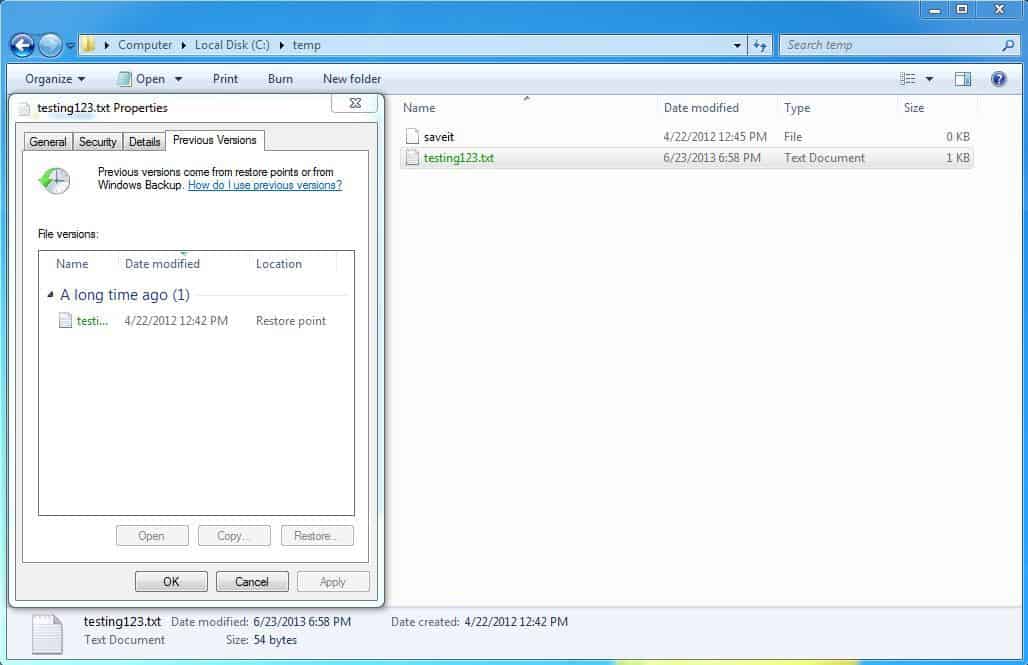
If you already have restore points created, then one method to recover and unlock a file is to use of the Restore Previous File Version feature in Windows Explorer. Launch Windows Explorer and open the folder containing the locked file. Alt-Click (right mouse button) on the file and select restore Previous Versions. If you have created a restore point, and the file has been altered, you may select it from the list of available file versions.
Once you have selected a file, you may open it and then relocate it using the Save-As option, copy it to an alternate location, or restore it. Restoring the file may not correct all file lock situations, though is a reasonable starting point.
System Permissions
When using Windows 7, don’t forget about file permissions and the role played by User Account Control.
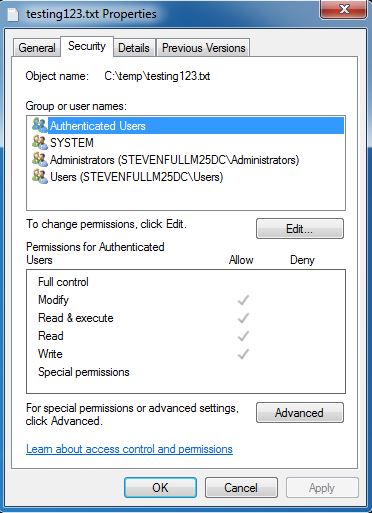
Even if you are a help desk technician or system administrator, if you are not the owner of a file you may not have the permission to modify, move, or delete a file when running as a standard user. When debugging file lock problems, make certain that you launch Windows Explorer by typing ‘Windows Explorer’ in the Search box, then use Alt-Click to Run as Administrator. If you merely launch Windows Explorer from the Quick Launch bar or by selecting Computer you will be running in Standard User mode.
Once in Windows Explorer you may check the file properties for Security settings including modify permission. You may also take ownership under the Advanced Settings button though want to be extremely cautious about taking Ownership in Windows 7, since this may disrupt the creator’s permissions. If the file is encrypted, NEVER attempt to take control unless your enterprise has an encryption recovery policy in place and validated.
You can also attempt the Previous Versions of Files option for file recovery through the file Properties panel.
File permissions can also affect server side folders. Remember that file security permissions are NTFS, not Operating System, based. You will need the File Server administrator to check file permissions if a file is locked on the server side.
If a user has locked a file through improper application termination on the client side, you may still be able to acquire a copy of the file from the file server. Copy is the key concept here. You will have to assist on the client (either locally or through remote access) to clean up any local %temp% files that may be preventing file access for the client.
Task Manager
If the file is locked due to improper application termination, you may be able to clear the file lock by locating the running process within Task Manager, and ending the process tree. Remember that you may launch multiple instances of a program as unique shells in Windows 7. Although you may be able to launch a second or third instance of Microsoft Word, for example, the locked file may be associated with process residue from an improperly terminated instance of the application. The Microsoft recommendation is to reboot the system, though we teach never to use a system reboot to solve a problem without justification. You want to do your research and confirm that a process is locking the file before rebooting. If the process is set to Auto-start or is part of a Startup group, merely rebooting the system will not resolve the problem.
While in Task Manager, you might also check to see if there are other users attached to the system. Concurrent or alternate use of the file is another cause for the file to be locked. Merely select the Users tab within task manager. You should only see one local session, and potentially one remote session if you are using Remote Desktop or Remote Assistance to debug the file issue.
Process Explorer
For a more sophisticated file diagnostic tool, you want to use the Microsoft Process Explorer from Sysinternals. You want to acquire it through TechNet.
Process Explorer will enable you to thoroughly research which files, handles, and DLLs are open or locked by a specific process. Process Explorer should help you to specifically identify why a particular file is locked.
NOTE: Make sure you have permissions to install applications on the client, and that you run the installation and run the tool as an Administrator. User Account Control does not typically want a standard user implementing a tool with this capability.
The Technet download site offers several links to other tools by Mark Russinovich, the tools author, as well as an administrator’s reference that may also be useful.
Use of Process Explorer to research a file lock problem is fairly straight forward. Joe Medeiros of Javelin offers a quick overview.
Slow Process Termination and Integration Tools
One other thought before I close this blog.
Several Windows 7 applications stay resident for minutes after they are closed. Even if you close them properly. For instance, Internet Explorer may continue to run for 5 or 10 minutes after you close all the Internet Explorer Windows.
If the application incorporates add-ons, uses Windows or Microsoft Update to receive updates and patches, or integrates multiple applications, then you may have to wait several minutes before you can access files that were locked during use by the application.
For instance, I keep Evernote running on my system to capture student questions, random thoughts, or articles I find while teaching or researching. Evernote integrates with my browser, mail client, Microsoft Word and other applications. If I snapshot file content and place it into Evernote, then the file may be marked as in use even after I close the initial application. With the growing number of workflow management and cloud based solutions deployed today, you will want to assure that you close all running applications and then confirm that they are closed using Task Manager before pulling your hair out identifying how a file may be locked.
As with all good troubleshooting efforts, isolation of the issue requires eliminating as many factors as possible, and that includes properly terminating all but essential applications during the investigative and repair process.
Now, go break that file lock!
Steven Fullmer
Interface Technical Training Staff Instructor
You May Also Like
A Simple Introduction to Cisco CML2
0 3896 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 642 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 727 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments