How to spiff up your banners in Cisco IOS
How to spiff up your banners in Cisco IOS
If you access your Cisco gear via vty (Telnet, SSH, …) here is a little jewel that you may appreciate. It won’t be on your CCNA R&S certification exam, but it has a coolness factor significant enough that I wanted to point it out. A typical remote login, when successful, will display the hostname of the device as the prompt. If you want to liven it up a little, and provide a bit more info to the one logging in, check this out:
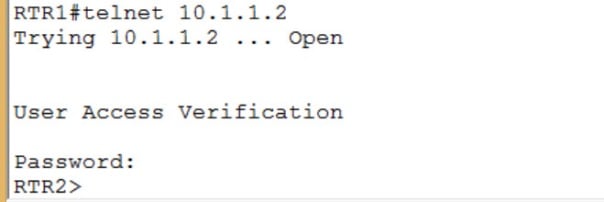
The command is banner. You are likely already familiar with the command, but don’t click on another tab yet. The coolness is seen by the person logging in. Let’s take a look. Figure 1 shows the normal view when logging in remotely to your Cisco device:
Figure 1
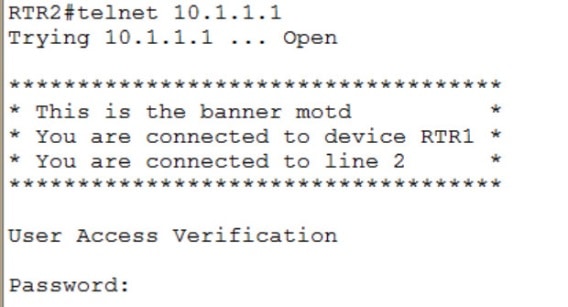
Well that was kind of hum-drum. RTR1 was able to successfully Telnet to RTR2. Whoopee. Now let’s see what RTR2 sees when it accesses RTR1, as shown in figure 2:
Figure 2
Now that is much better! I can’t tell the hostname (yet) from the prompt, because I am required to log in first. However, (assuming that I was aiming at RTR1) I can see in the banner motd that the host name of the device to which I am connected is RTR1. I also know on which line (line 2, as shown in figure 2) I am connected.
Can I survive without this feature? Certainly. But once you have practiced configuring all your lab gear in preparation for your certification exam, why not do a little IOS exploring and see what neat features are not mentioned in your courseware curriculum. But wait! I didn’t show you how it was done. Let’s take a look at the necessary steps.
The banner motd command is a common piece added to a configuration and, as you likely know, looks like this:
banner motd %
This command is entered in global configuration mode, and the percent sign is a delimiting character that lets the device know where the message starts. It can be any character that does not appear anywhere in the body of the message. I usually use a percent sign, but you can you any character you wish that fits the above stipulation. Now you can continue typing your banner message right after the percent sign, but I like it better if you type just the above command and hit Enter. Now you can enter line after line of text character that will comprise your banner. When you are finished typing the body of the banner, type your delimiting character once more so that device knows you are done with the banner.
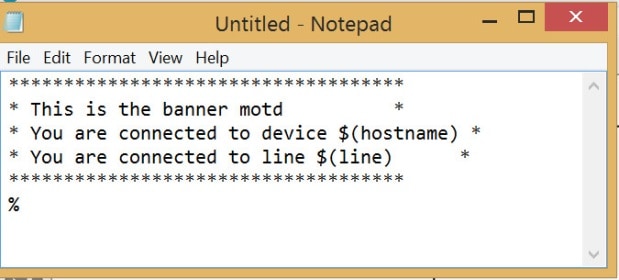
I usually construct my banners in some bare bones text editor (Notepad, Notepad++, VIM) so I can just paste it into the device. Then if I have formatting issues, I can modify my text file to adjust and then paste it in again. Figure 3 shows what I pasted to generate the output shown in figure2:
Figure 3
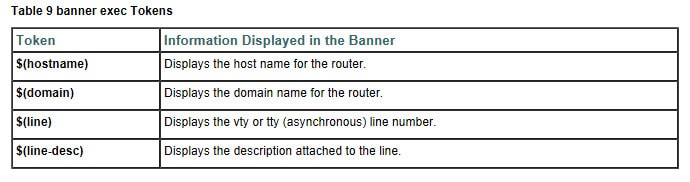
Now there are only a few of those options that are configurable. Cisco documents your choices in this regard. The table in figure 4 was retrieved from Cisco Connection, Menu, and System Banner Commands.
Figure 4
As you can see in my config, I used $(hostname) and $(line). As noted, you can survive a turbulent IT career and never type this once, but it adds some personalization as well as valuable information to the remote login scenario. If you have the inclination, type it and feel the rush!
Until next time…
Mark Jacob
Cisco and CompTIA Network + Instructor – Interface Technical Training
Phoenix, AZ
You May Also Like
A Simple Introduction to Cisco CML2
0 3896 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 642 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 727 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments