Sources of Interference and When You Should Be Concerned
Sources of Interference and When You Should Be Concerned
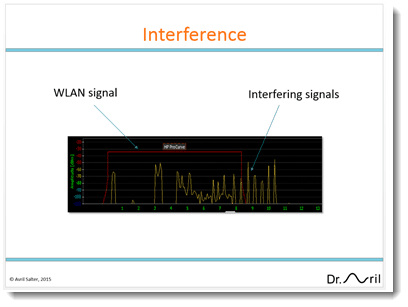
What is interference?
Wi-Fi operates in the license-exempt frequency bands. The main advantage of operating in these bands is that the network administrator does not need to pay a licensing fee to operate their equipment. The primary disadvantage of operating in these bands is that other equipment may also be transmitting in these bands, and could cause interfere with the operations of your Wi-Fi system.
Equipment that operates in the license-exempt frequency bands include Wi-Fi, Bluetooth radios, sensor networks such as ZigBee, microwave ovens, cordless phones, wireless Surveillance cameras, and satellites. Surveillance cameras can be particularly disruptive to Wi-Fi networks as they may be transmitting 100% of the time.
Interference negatively impacts performance
Before a Wi-Fi device transmits, it listens to the frequency channel. If it detects noise on this channel above a threshold defined in the 802.11 standards it will not transmit. When the wireless medium is free, the Wi-Fi device will then start its transmission procedures. Interference from devices operating on the same channel can therefore cause wireless transmissions to be delayed, resulting in a significant degradation to throughput and Quality of Service (QoS).
If the interference is bursty in nature, then a Wi-Fi device could transmit thinking that the medium is free, but the signal could be impacted while being transmitted over-the-air. This can lead to an increase in retransmission of lost packets, which in turn also detriments throughput and QoS.
Interference reduces coverage
Most IP Professionals understand that interference impacts throughput and QoS, however they do not realize the impact of Wi-Fi coverage. A good analogy for understanding the impact on coverage is to consider a conversation between two people in a restaurant.
If the restaurant is quiet with little noise and interference, you can easily have a clear and error free conversation. If the restaurant is noisy, you have to shout to be heard over the noise and you have to repeat your words more often. It also helps if you get closer to the person you are trying to talk with. In other words, in a noisy high interference environment, cell coverage is reduced.
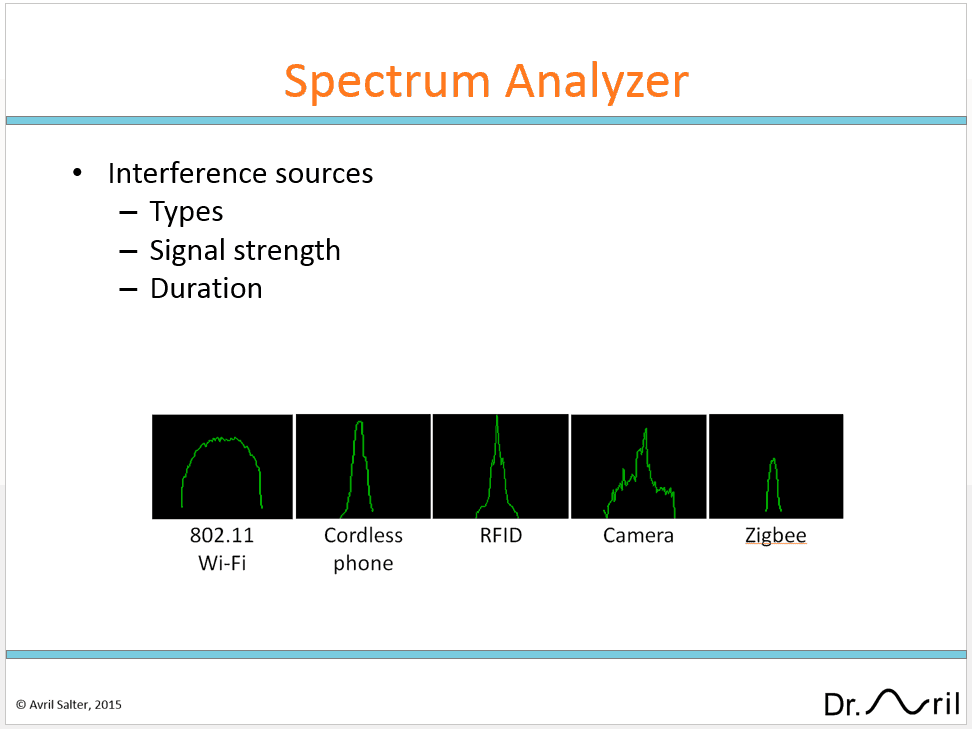
Detecting sources of interference
The best way to detect interference sources is to use a spectrum analyzer. Spectrum analyzers display all received signals in a selected frequency. Transmissions from Wi-Fi devices, microwave ovens, cordless phones and cameras have different transmission profiles. Some of these transmission profiles are illustrated in figure 3. By looking at the shape of the signals on the spectrum analyzer you can identify the probable type of interfering sources.
A spectrum analyzer can range in price from a few hundred dollars to thousands of dollars depending on the functionality. Indeed, many Access Points actually include spectrum analyzer capabilities. A simple low cost spectrum analyzer should enable you to both measure the received signal strength, and provide analysis on how the received signal strength changes over a period of time. This is important as it will tell you now the received signal strength is fluctuating during the day. Widely fluctuating signals warrant further investigation, as it is an indication that something is changing in the environment.
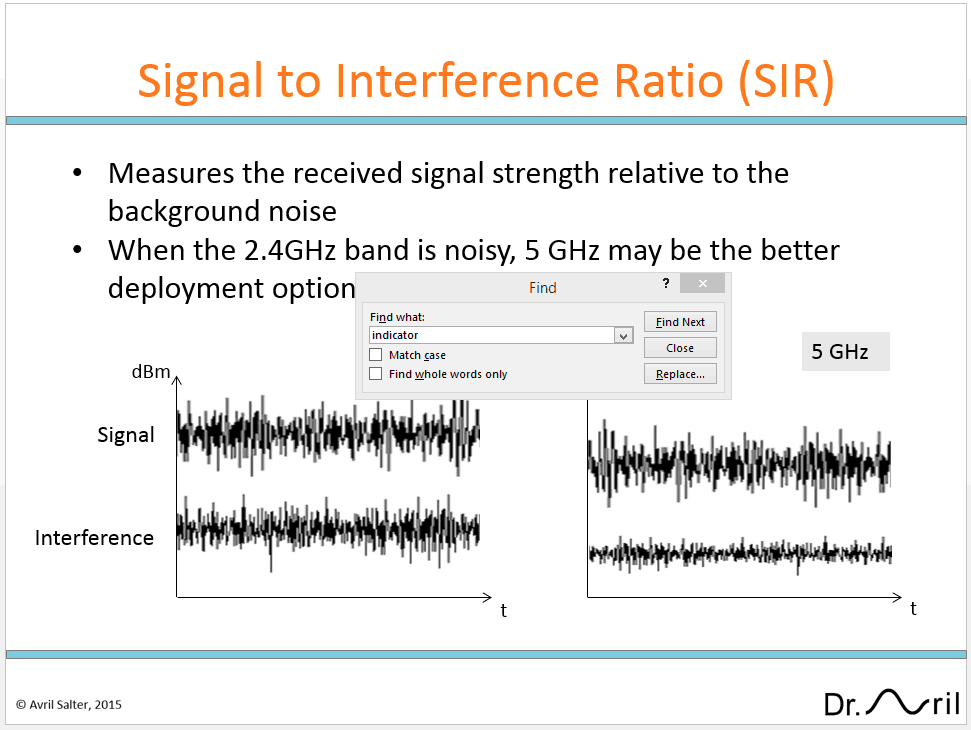
What is an acceptable level of interference
In order to successfully receive a signal, the transmitted signal must be heard above the interference. One of the key measurements IT professionals who are managing Wi-Fi networks need to understand is the Signal to Interference Ratio (SIR). The SIR is a measure of the received signal power level over the interference at the receiver. It indicates whether the received signal can be recovered at the receiver.
Typically for data applications you will want to make sure your received signal strength does not drop below -70 dBm. If you are implementing wireless phones, a higher threshold such as -67 dBm will be needed.
In most enterprise environments, interference is typically below -90 bBm. In other words, a SIR of 20 or 23 is generally considered good for data or voice applications, respectively.
Want to learn more?
Interface is offering a new course for IT professionals, to equip them with the skills necessary to plan, configure, troubleshoot and optimize Wi-Fi networks.
Register for this course today.
WIRE400: Wireless Networking for the IT Professional
5-Day course at Interface Technical Training in Phoenix, Arizona.
Learn how to take control of your enterprises Wi-Fi network. In this 5-day hands-on course, you will learn how to plan, configure, deploy and manage a wireless network, secure and troubleshoot interference sources, identify and analyze Wi-Fi packets in Wireshark for data transfer. This course finishes with an overview of the latest next generation in Wi-Fi product enhancements for enterprise and end-users.
You May Also Like
A Simple Introduction to Cisco CML2
0 3898 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Cable Testers and How to Use them in Network Environments
0 727 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments
Understanding Latency in Troubleshooting Network Connectivity
0 40 0This content is from our CompTIA Network + Video Certification Training Course. Start training today! Every one of us has experienced latency. Think about it, you’re on the internet streaming a video on YouTube and one second, the person of on the right of the screen then in the next consecutive second, the person have … Continue reading Understanding Latency in Troubleshooting Network Connectivity