This is NOT a Joke! Beware of IT Helpdesk Phone Scams
This is NOT a Joke! Beware of IT Helpdesk Phone Scams
Got that call that every IT expert fears; A client succumbs to a hacking scam and wants you to make everything right. Immediately.
My friend left three voice mails in a five minute period. I needed to call. A helpdesk technician had called to help with their system and everything is missing.
Long time friend, so I called back. I started with that friendly reminder. My portion of the dialog is indented.
“Unless you initiated the call, there is no Zen helpdesk that knows you need help with your technology. Not your PC or phone or Internet router. Did you call or did they call you?
Microsoft called me. They knew my system was running slowly and were so friendly and helpful and knew I had Windows 8.1
Really? For free?
They didn’t want a credit card number or money. Just access to my PC to help me.
Did you let them have access?
Yes, they told me how to let them access my system remotely. They were the Microsoft helpdesk from India. Since I couldn’t understand what they were suggesting, I let them have access. It only took them 30 minutes and they had my system repaired.
Did you watch what they were doing on your system?
No. They told me what they were doing while I listened on my phone. They told me the system was infected by the “Har Har Mahadev” virus.
(Unfortunately, I could see them chuckling ‘har har har’. ) I looked up the virus. Har Har Mahadev is a famous Bollywood Movie from 1950 about Shiva and his indecencies. Ouch. No such virus.
And what are the symptoms that caused you to call me?
When I login, there are no icons on my system and I can’t find any of my files. But it boots faster.
(I bet it does). Sorry, my friend, but system recovery is the least of your worries. They have all of your data.
You mean all my accounts and bank information and everything?
Yes, if it was on your system, they have it.
What do I now?
Call all of your banks and let them know before you do anything else.
But I don’t have my files.
Pause in conversation…
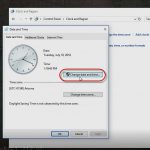
At this point, I walked him carefully through a System Restore process. We were able to use a recovery point just a few days old. The system appeared restored once we restarted.
I then pointed him to a Microsoft website that explains the scam (somewhat), and the detailed steps necessary to continue the recovery process.
From Answers.Microsoft.Com regarding Phone Call Scams.
I am not going to repeat the process that my friend needs to take. A few highlights follow.
- The best action is to isolate your assets – particularly your financial ones – as quickly as possible. Notify the banks. Notify the authorities.
- The specific value of creating the restore point was to provide access to account and contact information.
- Never save personal or account information on your system except in a digital vault or encrypted format. Back up account and personal information and store it in a physically secured location. Get it off the system before you attempt to validate any other functionality. Do it without a network or Internet connection. You have no idea how long you might have before a Logic Bomb (time, event, or action based) destroys everything on your system beyond recovery.
Once your personal information and identity is recovered, rebuild you entire system from scratch, starting with your OS, and including your applications and data files. There is no sure or secure way to identify the residue these hackers left. Their access was equivalent to sitting at the keyboard with administrative rights and the tools to take or leave any binary content they desire.
If you are willing, you can deliver your system into the hands of the authorities to see if they can find evidence for prosecution. Although recovery or compensation is unlikely. The best you might achieve is stopping these hackers form hurting someone else.
Hence this blog.
Don’t let it happen to you or someone you know. Share this with everyone you know.
Or redirect them to an article from the Better Business Bureau.
The scams are getting more sophisticated, bold, and realistic. As technology becomes more simplified for the end-user, lack of awareness will continue to create opportunities for hackers with slightly more knowledge.
Awareness and education are the first line of security defense.
I look forward to seeing you in the classroom, or online!
Steven Fullmer
Interface Technical Training Staff Instructor
Steve teaches PMP: Project Management Fundamentals and Professional Certification, Windows 7, Windows 8.1 and CompTIA classes in Phoenix, Arizona.
You May Also Like
hacker, har har mahdev, identity theft, Malware, phone scam, protect, re-image, Recovery, remote access, Restore point
A Simple Introduction to Cisco CML2
0 3894 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 642 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 725 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments

See what people are saying...