Using WHOAMI.exe to troubleshoot NTFS Permissions
Using WHOAMI.exe to troubleshoot NTFS Permissions
See our class schedule for complete Windows 7 and Server 2012 Training.
Classes are held in Phoenix, AZ and can be attended online from anywhere in the world with RemoteLive™.
Instructor: Rick Trader
Video Transcript:
One of the most common problems you will run into as an IT administrator when working in an enterprise or a domain environment is when a user attempts to access a resource and receives a message stating “Access Denied”. Or visa-versa, a user is able to access a resource that they shouldn’t have access to.
WHOAMI.exe is one of the tools that I like to use to help me troubleshoot user NTFS permissions. This is a tool that a lot of us administrators have over-looked for years.
Here’s how to use WHOAMI.exe and some of its switches.
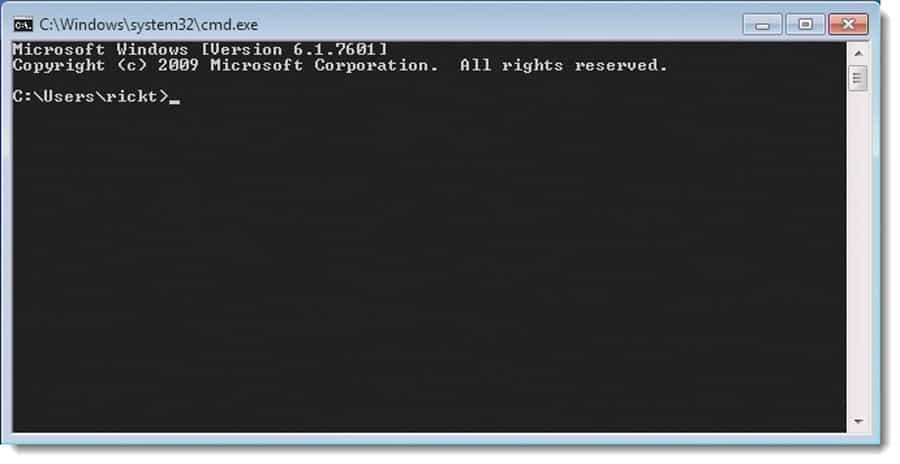
Starting at my command prompt and logged on as the user.
As a Help Desk person, I can have the user on the phone and bring up their command prompt or I could remote desktop with them with any of the corporate tools that you may already have that allows you to connect to them or you can have the user do this over the phone by having them launch a command prompt and have them type [whoami].
Most of us administrators in the IT industry already know about this command, we’ve used it frequently to determine whether the user is logged on with the appropriate credentials. You can find out if they’re logged into the domain and to see if they’re logged into the machine.
{01:09}
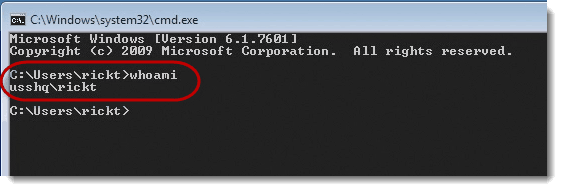
A switch that many people don’t know is “whoami forward slash all” whoami /all
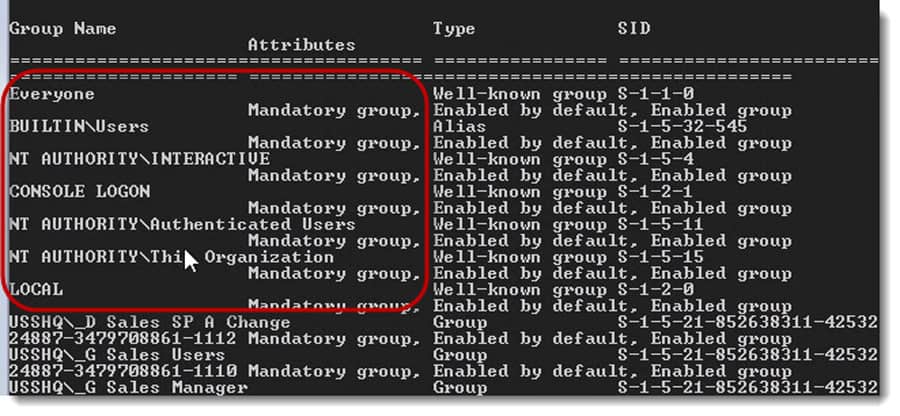
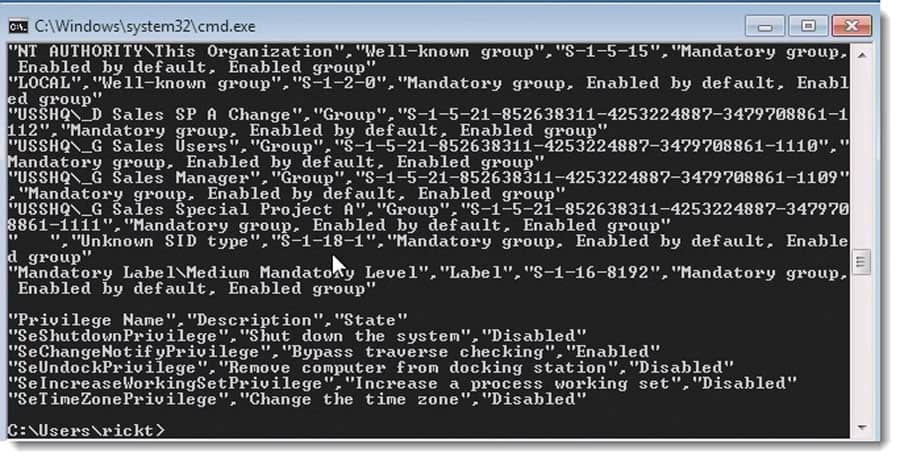
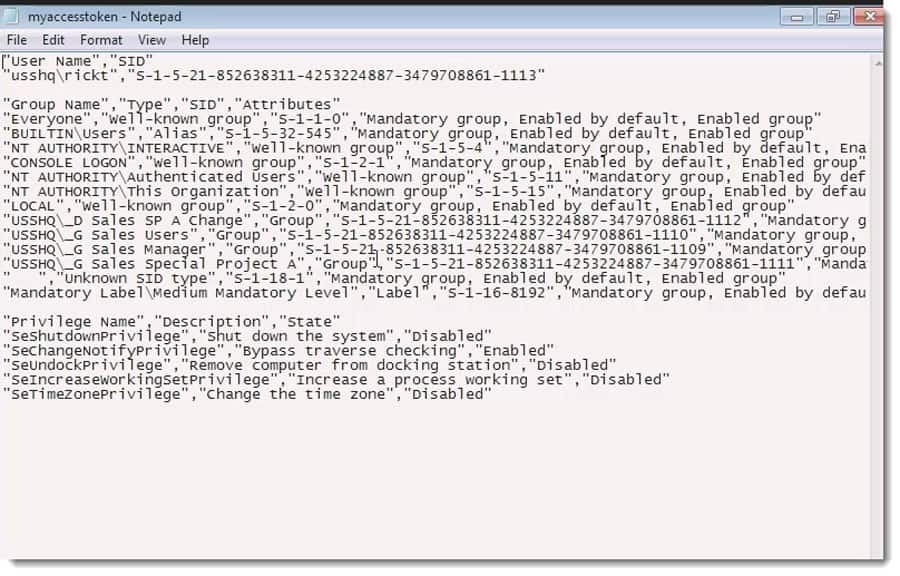
This switch will show me not only who I’m logged in as but it will also show me my current user SID and it also shows me the Groups that I am currently a member of.
In other words, it’s showing me my current access token. In Windows NT 4.0 and Windows 2000, you may have heard of a utility called “MYTOKEN.exe”. You could download it and accomplish the same thing.
In Windows 7, it shows me that I’m a member of groups. For example, Everyone, Users, Console Logon, Authenticated Users etc… These are all the built-in groups and local groups.
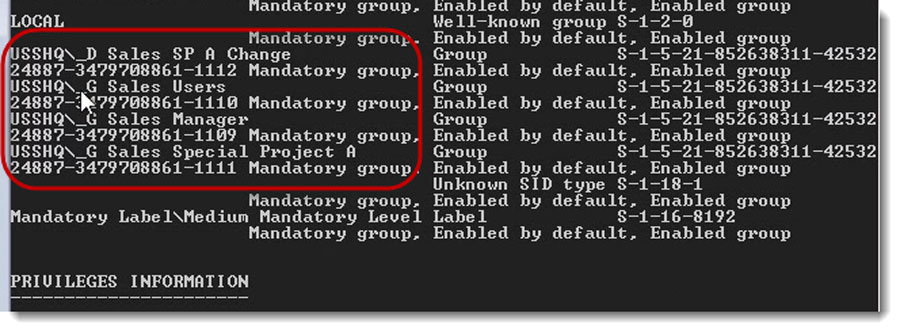
But notice; it also shows me that I’m logged on as “rickt” and that I’m a member of a group called [_D Sales SP A Change] , [_G Sales Users] [_G Sales Manager] etc…
WHOAMI is displaying all the groups I’m currently a member of in standard naming conventions. I.e. “_D” is a Domain Local Group while “_G” is a Global group. Therefore, I know that the “_G Sales Special Project A” is in the “SP A Change” folder.
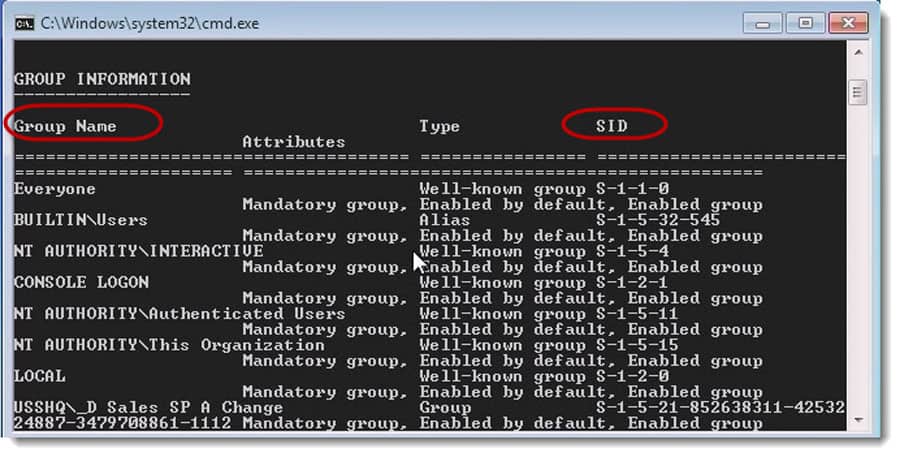
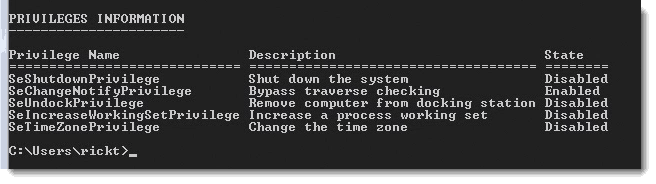
WHOAMI /all also shows me the privileges I currently have on this machine.
You’ll notice the “Change the time zone” requires elevated permission levels to do this and it’s displaying the state of “Disabled”. Others are also Disabled such as “Shut down the system”. Therefore, when you try to shut down, it’s going to ask you for elevated privileges.
The big concept is that it’s showing me the groups.
{02.57}
Many students have asked me “How long has whoami / all been around?” It’s been available in Windows XP, Windows 2003, Windows 2008 & 2008 R2, Windows 7, Server 2012 and now in Windows 8. They all have the whoami.exe command. It’s an awesome command available for troubleshooting.
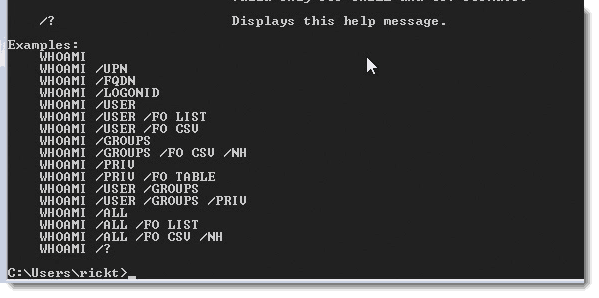
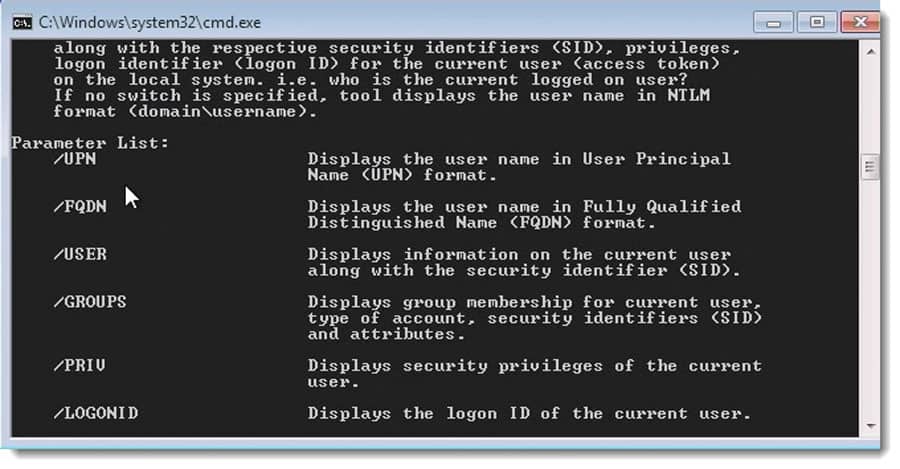
There are a couple additional switches in “whoami.exe”.
If we use the question mark: whoami /?
I can show my logon information and parameters such as:
/UPN – User Principle Name
/FQDN – Fully Qualified Distinguished Name
I can show just my USER SID or Just my Group SID
/PRIV – Privileges
/LOGONID – Is an option if my logon id is different than my user ID.
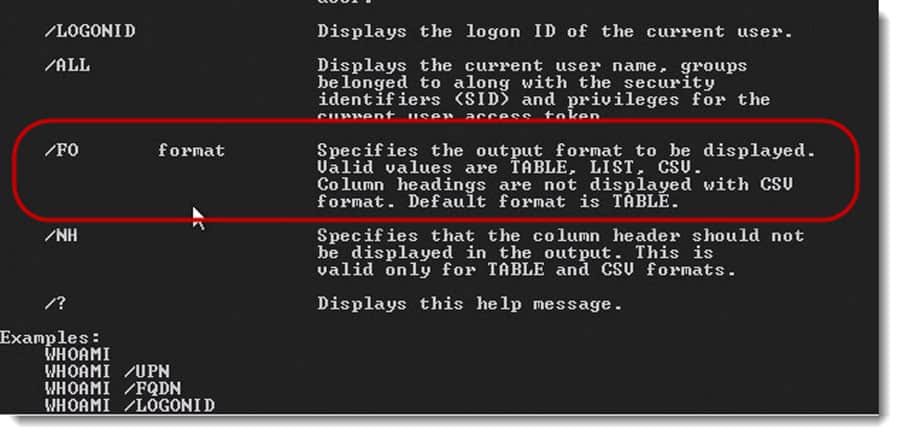
We can also format with the /FO option and format it as a table, list or a CSV.
{03:47}
If I format it as a CSV
Using “FO” Format Out
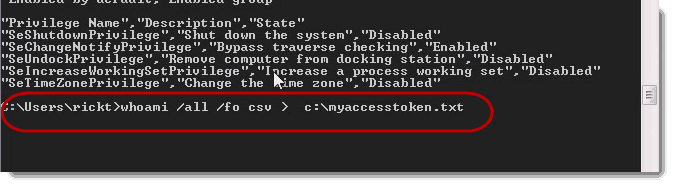
whoami /all /fo csv
Notice that it did format this as a coma separated values CSV file. Notice the comas between each field?
If you wanted to output this to a file you would need toe pipe it “|” out or perform the typical “out” such as [C:\myacccestoken.txt]
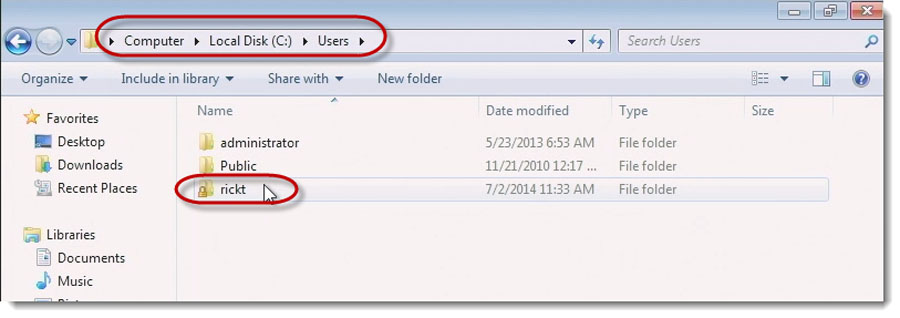
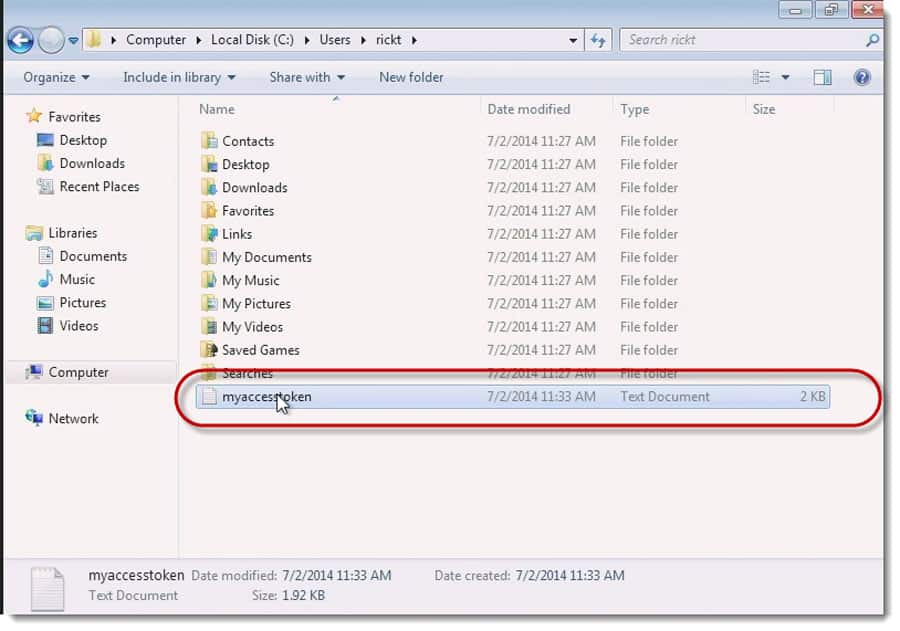
This outputted to a text file. If I go into Windows Explorer and look into the user folder:
Select my folder which is names “rickt”:
The file is located:
And here is the coma separated values CSV file:
Having it in a text file allows the user to troubleshoot much easier.
One of the changes that is made to this if you’re looking at whoami from Windows Server 2012 or a Windows 8 computer is underneath privilege name you will see an area called “Claims”. If you’re doing Claimed-Based Authentication this will show you your claims.
I hope this has helped you with troubleshooting NTFS Permissions and determining what a Groups a particular user is a member of.
Until next time, ride safe.
Rick Trader
Windows Server Instructor – Interface Technical Training
Phoenix, AZ
You May Also Like
A Simple Introduction to Cisco CML2
0 3896 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 642 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 727 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments



See what people are saying...