Walk softly and carry a Router-on-a-stick! (ROS)
Walk softly and carry a Router-on-a-stick! (ROS)
So you are maintaining a medium-sized network and you want to route traffic between your VLANs. What are your options? You can place one router interface in one VLAN and another router interface in each of the additional VLANs, but this is horribly inefficient use of router resources. Another option is to use Layer 3 switches to move traffic between your VLANs. While this is quite efficient and widely used, it is not a topic included in the ICND curriculum. For this reason, I will skip to option 3, also known as Router-on-a-stick (ROS).
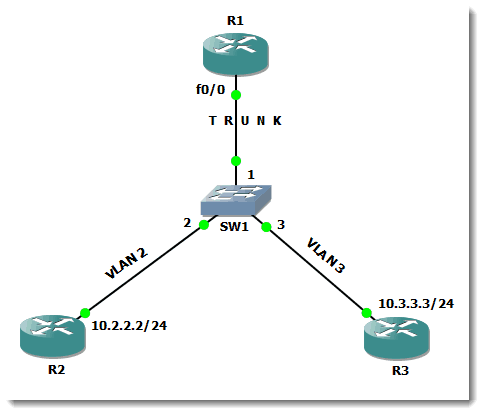
I recently had a student in my class who mentioned that he heard that the term Router-on-a-stick was losing favor. I was shattered by this news. So many terms in IT are dry and unentertaining, so this one deserves its place in the network admin’s lexicon. That being said, let’s examine the network scenario and configuration for which ROS will fill the need. Here is a network diagram for the configuration that will appear in this blog:
R2 and R3 are really just IP endpoints in this scenario – you can even imagine them as IP hosts. R1 is the router that will be assuming the role as the router on a stick. VLAN 2 and VLAN 3 are already configured on SW1. Since the topic of this blog is routing between VLANs, we can’t forget the necessity of the trunking link between the switch and the ROS router, R1. This configuration is standard on a switch for creating a trunk and is shown here:
SW1 (config-if)#switchport trunk encapsulation dot1q <- necessary on some switches
SW1 (config-if)#switchport mode trunk
SW1 (config-if)#speed 100
SW1 (config-if)#duplex full <- it is a good idea to hard-code speed and duplex on trunk links
Good practice would also include limiting which VLANs are permitted to cross the trunk link. Here is the syntax:
SW1 (config-if)#switchport trunk allowed vlan 1,2,3
The rest of the necessary configuration must occur on R1. Let’s take a look:
R1 (config)#interface FastEthernet0/0
R1 (config-if)#no ip address
R1 (config-if)#speed 100
R1 (config-if)#full-duplex
R1 (config-if)#interface FastEthernet0/0.1
R1 (config-if)#encapsulation dot1Q 1 native
R1 (config-if)#ip address 10.1.1.1 255.255.255.0
R1 (config-if)#interface FastEthernet0/0.2
R1 (config-if)#encapsulation dot1Q 2
R1 (config-if)#ip address 10.2.2.1 255.255.255.0
R1 (config-if)#interface FastEthernet0/0.3
R1 (config-if)#encapsulation dot1Q 3
R1 (config-if)#ip address 10.3.3.1 255.255.255.0
On the ‘real’ interface, remove the IP address (if one exists), hard code the speed and duplex (to match the switch), and the rest of the configuration goes on the subinterfaces. You will notice that the subinterface numbers that are in the above configuration match the number of the VLAN. While this is not a requirement, it sure makes troubleshooting, as well as following the logic, much easier. The ‘encapsulation’ command creates a VLAN on each subinterface on the router using the dot1q trunking protocol. Each subinterface requires an IP address in the range of the VLAN with which it is associated. This address will also serve as the default gateway address for the hosts in the VLAN.
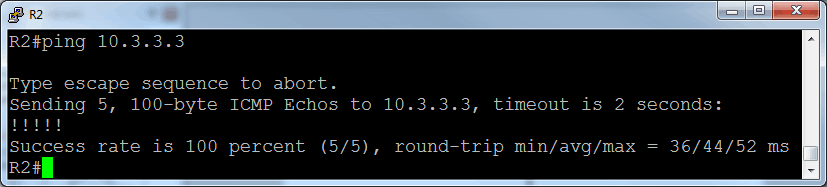
Now that this configuration is in place, it is wise to verify functionality. Let’s do that by attempting a ping from R2 to R3:
As you see, the configuration is not particularly difficult, and this solution is quite viable for small to medium networks. Once your network scales to LARGE, you will probably migrate to Layer 3 switches for your inter-VLAN routing solution.
Until then, enjoy configuring, and saying, router-on-a-stick!
Mark Jacob
Cisco Instructor – Interface Technical Training
Phoenix, AZ
You May Also Like
dot1q, encapsulation, ROS, router-on-a-stick, trunk, trunking, VLAN
A Simple Introduction to Cisco CML2
0 3901 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 643 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 731 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments




Pingback: CCNA Route & SWitch prep, GNS3 1.x, and Router-on-a-stick!