Windows 10 – Exploring Security
Windows 10 – Exploring Security
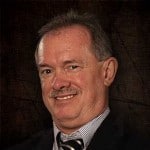
I continue my exploration of Windows 10. Ran an update first thing this morning, and received updates requiring a reboot. Not much information about the update contents when looking at Advanced Options within Windows Update settings.
Still not much in terms of the App Store either. In fact, I could not get the App Store to launch in Windows 10. I confirmed that my Microsoft account and domain account are synchronized in my settings. Then confirmed UAC settings are as suggested for Windows 8.1 and that screen resolution is 1366×768 (the minimum for Store Apps and snap capabilities.) I then ran wsreset.exe from the Search bar and succeeded in getting the Store Application to launch. Still no ability to launch the Microsoft Store. I continue to receive the 0x80072f8f error code. I am not ready to use advanced Windows 8.1 troubleshooting to get Windows 10 technical evaluation to work. I could try the Cleanboot solution for the above error code as promoted by KB929135 – How to perform a clean boot in Windows, though don’t want to damage my Windows 10 evaluation copy with experimentation until I have explored its base capabilities further.
So let’s look into some of the security features.
Microsoft provided an overview of Windows 10 security in an October 2014 blog: Windows 10: Security and Identity Protection for the Modern World. It truly is merely an overview, though gives me a starting point for some investigation. NetworkWorld – Windows 10 security, privacy and manageability features clarified some of the security, including a disclosure regarding data capture capabilities that Microsoft placed within the technical preview to assist with their debug efforts. I am glad I read this article and am NOT performing my evaluation on a system that I will use everyday.
In summary: Security elements appear to include identity protection, access control, information protection, and threat resistance.
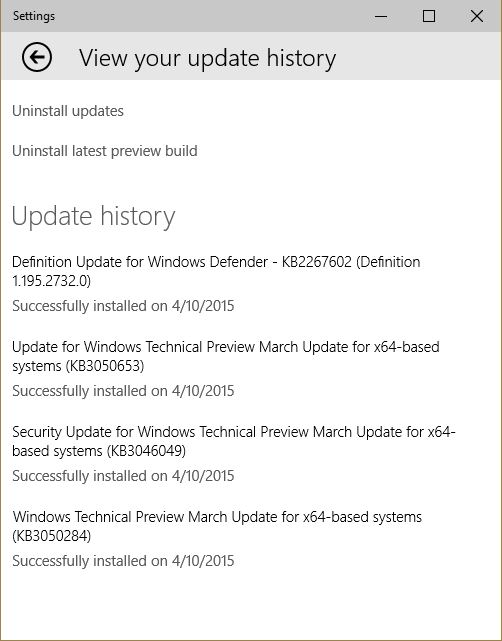
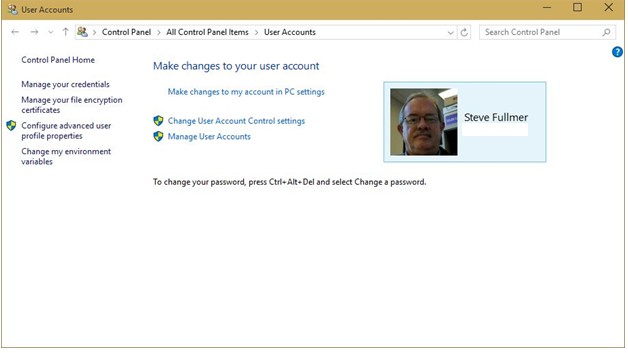
Identity protection includes migration toward multi-factor authentication (and away from simple account/password access); while access control expands the separation privilege levels and rights begun by the introduction of User Account Control in Windows Vista. The approach appears to be merely an evolution of the tools and concepts that were expanded within Windows 7, including a more navigable Credential Manager interface, and integrated more automatically within Windows 8.1. I do like the interface, with access to most account tools from a simplified interface on the control panel.
Selecting to make changes to my account via PC Settings takes me directly to a Charms-like application, with an all-in-one interface.
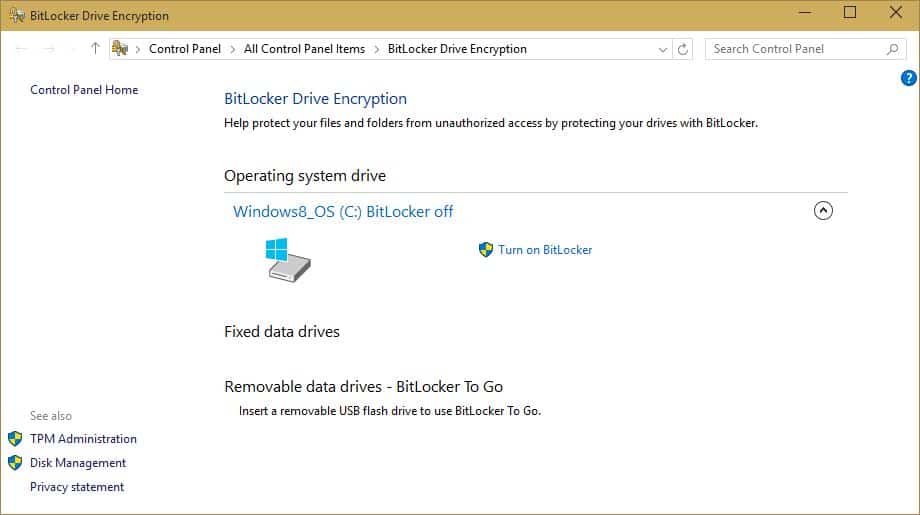
Information protection includes expanded digital signature capabilities; expanded drive (Bitlocker), folder, and file encryption capabilities; and enhanced backup and recovery alternatives. Again, an evolution of the concepts and alternatives introduced within Windows Vista and growing toward Windows 8.1. The capabilities are being expanded for integration into Azure (cloud) based solutions including Azure Rights Management and capabilities delivered with Office365. VPN capabilities are also being expanded.
I did not find anything significantly different in terms of the interface for Bitlocker or Bitlocker Management.
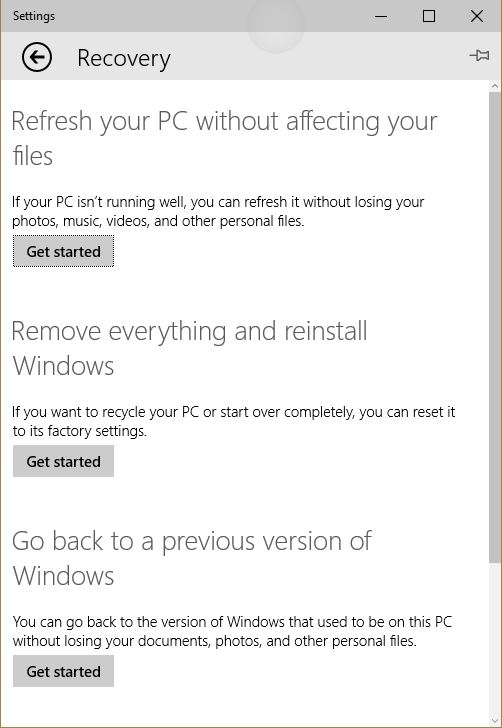
File encryption continues to utilize the EFS interface through File Manager. Backup and recovery options remain the same as Windows 8.1, including the Advance Boot capabilities (just below the border of my screenshot.)
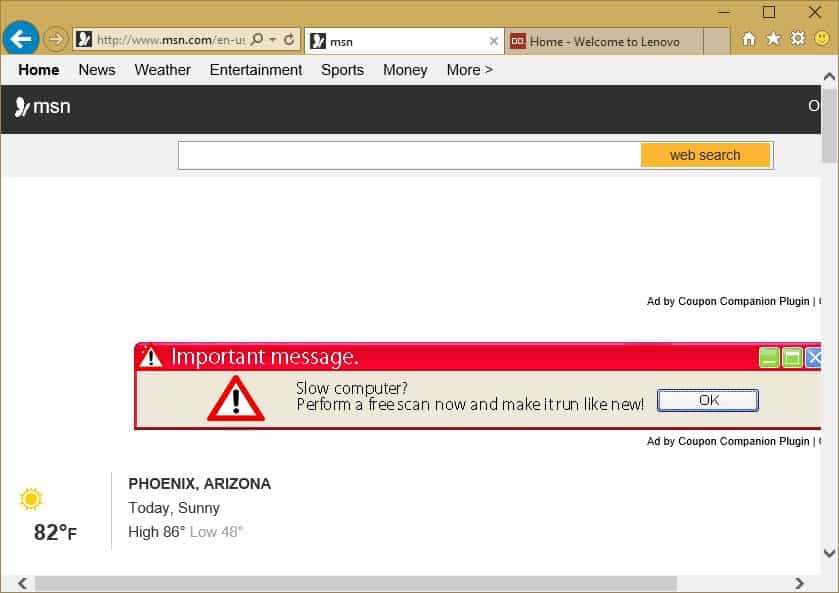
Threat resistance includes an enhanced browser (something different that Explorer 11 which was provided with the Windows 10 technical preview), expanded anti-malware provisions, and further hardening of the Operating System. Threat resistance will also be enabled by the ability to enable only applications trusted by the Microsoft signing service.
The technical preview incorporates IE11, and it’s launch tempted me with a third party add-in, so no significant changes here, at least not yet.
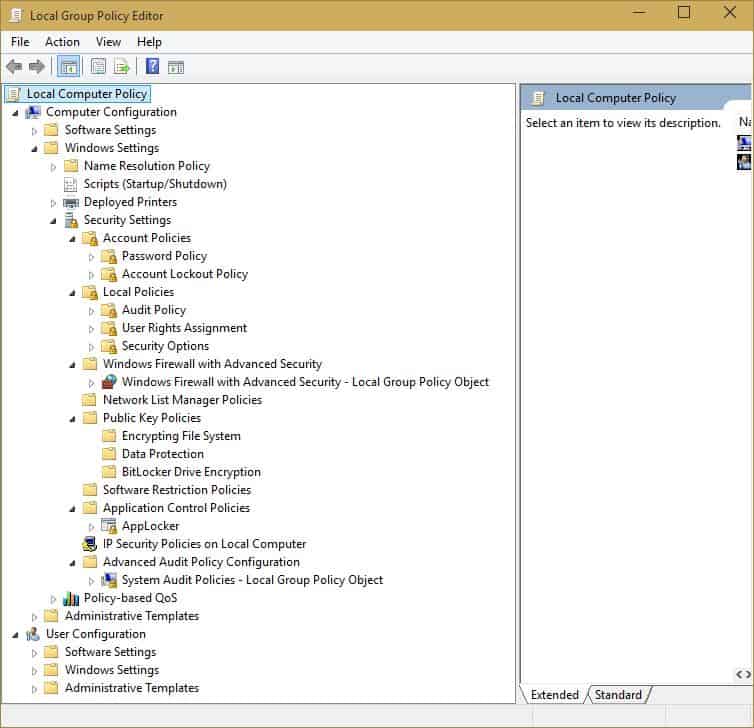
Most of the changes appear to be ‘under the hood’ as Microsoft proposes, so I decided to look at the Local Group Policy Editor. No obvious changes here either, since the options provide comparable Windows 8.1 features.
I suspect that threat resistance will include the enhancement of Windows Defender, which incorporated Anti-virus elements from Security Essentials within Windows 8.1. Aside from the signature update, the Windows Defender instance on my Windows 10 system closely resembles the appearance of the Windows 8.1 version.
Features continue to be announced in better detail, albeit slowly and more apparently for marketing than test or evaluation purposes. Promised features include expanded multi-factor authentication, a totally new browser (codenamed Spartan), and stronger component authentication/trust capabilities. Some of the trust capabilities include digital signatures for applications. Recall that Windows 8.1 enforced digital signatures for all drivers within both the 32-bit and 64-bit environments. The challenge of this latter component required third parties to comply with Microsoft signing authorities. The days of self signed component drivers within Windows 8.1 are near extinction. The promise to enforce digitally signed applications generates a potential to limit the participation of application providers for Windows 10. More secure, though less robust offerings in the application arena.
I will continue to monitor and test Security components. Meanwhile, you might want to explore the insights offered by a few other reviewers and Microsoft bloggers.
In December 2014 Windows Security.com expanded the table originally provided by Microsoft in October that summarizes Windows 10 promoted security features: Windows 10 – Privacy and Security Features at a Glance (Part 1).
The most recent article that I could find was published by SecurityWatch in January 2015: Windows 10: What’s new in Security.
In keeping with Microsoft’s current theme, it appears that much of Windows 10 security will be an integration of existing technologies, with reliance on central controls like Active Directory or Azure (and its Active Directory element). This is also consistent with Microsoft promotion that Windows 10 will provide common security controls across hardware platforms including the Windows Phone, tablet and PC platforms. True portability of data, accounts, and controls – as long as the key elements are integrated via a central or cloud based solution.
Hope to see you in the classroom or online!
Steven Fullmer
Interface Technical Training Staff Instructor
For more Windows 10 articles, see the following posts from Interface Technical Training:
- Windows 10 DVD Player Released by Rick Trader
- Where did my Windows Media Center go and what’s new in Windows 10? by Rick Trader
- Performing a Windows 10 Clean Installation using Windows 10 Upgrade Media by Rick Trader
- How to create Windows 10 Alternate Upgrade Media by Rick Trader
- Is the Windows 10 Upgrade Notification Malware? By Mike Danseglio
- Introducing Windows 10 for IT Professionals – Free eBook from Microsoft
- Windows 10 – Exploring Security by Steve Fullmer
- Windows 10 – “Recommended” Update enables Get Win 10 capabilities by Steve Fullmer
- How to Install the Latest Windows Update Agent by Steve Fullmer
- Windows 10 – First Look by Steve Fullmer
You May Also Like
0x80072f8f, access control, application signing, Azure, Azure Rights Management, backup, Bitlocker, Bitlocker Management, digital signatures, EFS, identity protection, information protection, KB929135, Local Security Policy Editor, Microsoft Account, Microsoft Store, multi-factor authentication, Office365, PIN, Recovery, Restore, Security, Spartan, threat resistance, User Account Control, VPN, Window 10, Windows Defender, Windows Update
A Simple Introduction to Cisco CML2
0 3896 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 642 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 727 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments




Pingback: Windows 10 - How to Change the Default Folder when launching File Explorer
Pingback: Windows 10 DVD Player Released
Pingback: Windows 10 – “Recommended” Update enables Get Win 10 capabilities
Pingback: How to Install the Latest Windows Update Agent
Pingback: Is the Windows 10 Upgrade Notification Malware?
Pingback: Windows 10 – Release Slated for July 29
Pingback: Introducing Windows 10 for IT Professionals - Free eBook from Microsoft - Interface Technical Training – Blogs