Wireless Networking for the IT Professional. Now Available at Interface Technical Training
Wireless Networking for the IT Professional. Now Available at Interface Technical Training
Why IT professionals need to understand wireless
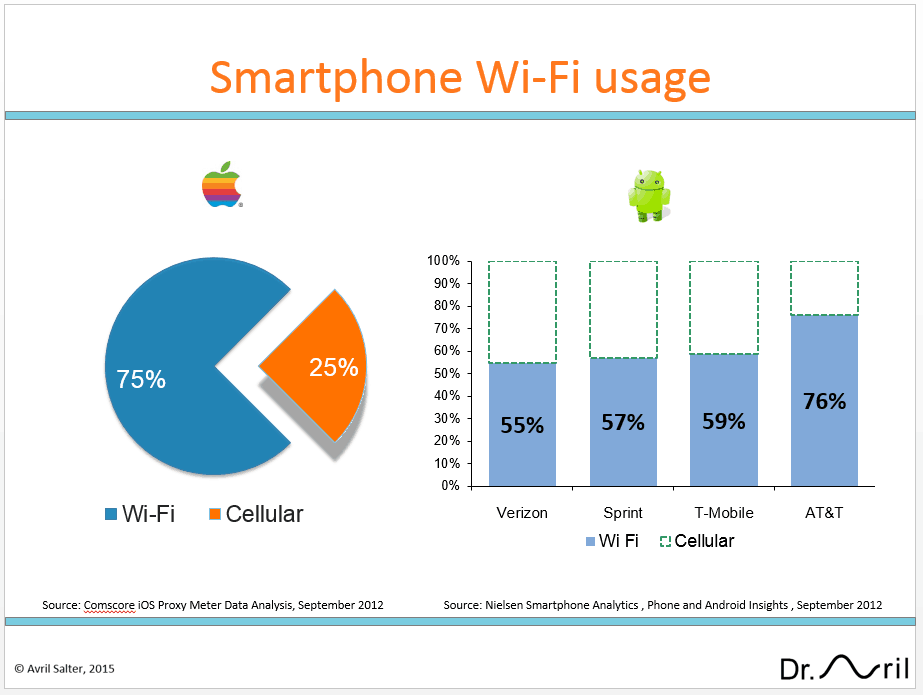
Wireless networks are becoming increasingly more important to all organizations, from mall mom and pop stores, to major corporations. It is forecasted that by 2018 wireless devices will account for 61% of IP traffic, greatly exceeding traffic from wired devices, which will reduced to a mere 39% of IP traffic. Cisco Visual Networking Index: Global Mobile Data Traffic Forecast Update, 2013–2018. The growth in smartphones and tablets connected to Wi-Fi networks has taken the industry by surprise. Today, smartphones send over 4 times more data over Wi-Fi than cellular, and these figure are set to grow. This has led to many organizations implementing “bring your own device” (BYOD) policies, to allow employees to connect their personal devices to the enterprise network.
As wireless networks become increasingly prevalent, it becomes critical that IT professional have a rudimentary understanding of wireless networks. With this in mind, Interface is offering a new course offering titled “Wireless for the IT Professional”.
What is exceptional about this new course offering?
There are three things that make this course exceptional: A world-renown instructor, a course syllabus that focuses on the IT lifecycle, and a unique opportunity to discuss and resolve real world problems
World-Renown Instructor:
Dr. Avril Salter has worked on Wireless LANs since 1992, five years before the first 802.11 Wi-Fi specifications were finalized. She developed her in-depth understanding of wireless while working for Motorola. Since then she has worked for Intel and Microsoft. She has taught Wi-Fi courses at Cisco since 2002, and has published an advanced wireless certification book with HP Press. Dr. Salter is well known for her ability to solve some of the most complex Wi-Fi implementation challenges.
What You Will Learn:
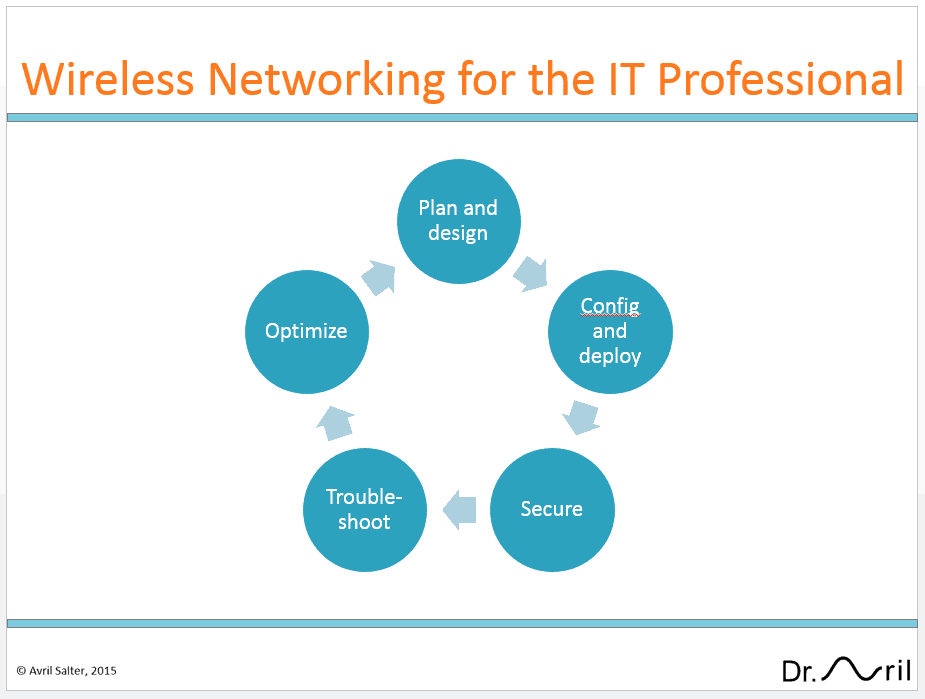
The course is focused around the IT lifecycle. This is distinct from other wireless courses which focus on certifications or how to implement a specific vendor’s wireless products.
The course starts by making sure the learner understands the radio concepts essential for planning and designing a wireless network. Key concepts range from assigning channel frequencies to determining sources of interference and calculating link budgets. It takes the learner through Wi-Fi operations including Quality of Service (QoS), equipping them with the knowledge to enable them to effectively configure Wi-Fi for their specific work environment Wireless brings the advantage of flexibility, convenience and improved productivity to the organization, but it comes with risks such as eavesdropping, unauthorized access, and rogue Access Points. For that reason, learners will walk through the different security options available for Wi-Fi networks and discuss how to select the right security mechanisms for an enterprise’s unique needs. Students will experience different types of wireless attacks, such as eavesdropping, Denial of Service (DOS) attacks, and Rogue Access Points (APs). They will learn how the Wi-Fi mechanisms provide (or do not provide) countermeasures to obviate these attacks.
Students will learn the best practices for troubleshooting wireless networks. Learners are given real-life problems and will be expected to use the tools and techniques used in the course to troubleshoot and identify these problems. Tools include the use of Wireshark to analyze wireless packet captures and a spectrum analyzer to assess interference and physical layer activities.
The course ends with a discussion on how high data rates and high capacity networks can be achieved and sustained in a live environment. Both 802.11n and the newer 802.11ac technologies will be covered in depth.
Real-World Problems:
Students are encouraged to bring into the classroom their wireless issues, for discussion and resolution. The instructor, Dr. Avril Salter, will guide the student in taking the material they are learning through the week and applying it to these real-life problems.
This technique not only reinforces the students learning, but most importantly enables the student to immediately be more effective in their job function.
Register for this course today.
WIRE400: Wireless Networking for the IT Professional
5-Day course at Interface Technical Training in Phoenix, Arizona.
Learn how to take control of your enterprises Wi-Fi network. In this 5-day hands-on course, you will learn how to plan, configure, deploy and manage a wireless network, secure and troubleshoot interference sources, identify and analyze Wi-Fi packets in Wireshark for data transfer. This course finishes with an overview of the latest next generation in Wi-Fi product enhancements for enterprise and end-users.
You May Also Like
A Simple Introduction to Cisco CML2
0 3896 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Cable Testers and How to Use them in Network Environments
0 727 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments
Data Models in Business Analysis
0 200 0This video is from our PMI-PBA Business Analysis for IT Analysts and Project Managers (PMI-PBA)® Certification now available at Interface Technical Training. Also see Steve’s PMP Project Management Certification Course: Project Management Professional (PMP®) Certification Video Training PMBOK® 6th Edition Video Transcription: Data Models are part of the elicitation analysis in PMI-PBA. This is the way … Continue reading Data Models in Business Analysis