Cisco Supernetting – Subnetting for Networking Professionals
Cisco Supernetting – Subnetting for Networking Professionals
Now that you have had time to digest the Cisco subnetting articles:
- Subnetting – Folding the Paper
- Advanced ‘folding the paper’ subnetting concepts
- Folding for Subnetting Professionals – subnetting a subnet and number of hosts per subnet
Let’s add another piece to the networking pie. If you have manipulated ones and zeros until you can subnet like a guru, then this should be just one small step for you. Supernetting, which can also be thought of as giving a router the ability to summarize multiple routes in a single announcement, is just another way to analyze the on and off bits in IPv4. Let’s see how it’s done.
The whole idea behind supernetting is comparable to looking at the CliffsNotes version of a book instead of reading the whole book. Why should a router announce everything it knows one at a time when it can more efficiently and quickly convey the same information with less? To understand this topic in detail, it does help, once again, to look at what’s going on behind the curtain. In this case, the curtain is the binary numbering system and what’s going on is we are adjusting where the stream of ones ends.
When subnetting, we slide the ending position of the stream of ones to the right. In supernetting, the reverse is true. We are sliding the end position to the left. For instance, if we are working with a Class B address of 172.16.0.0 with the default subnet mask, there are sixteen ones in the subnet mask in binary. If our router announces 172.16.0.0 /16, it is just announcing this entire classful network. So it is one network with 65,534 possible host addresses. A Class B network which has undergone supernetting will have a mask with fewer than sixteen ones lit up. Let’s take a look at it in action: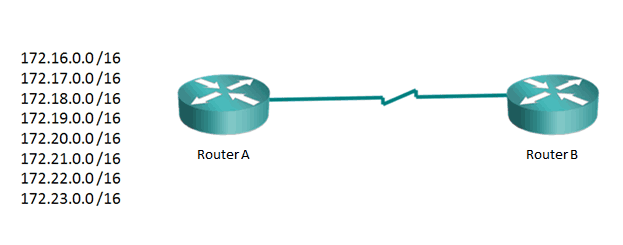
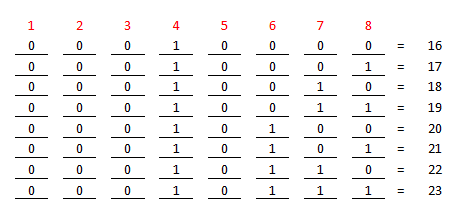
Now we want to know what Router A can announce to Router B regarding the routes behind Router A. If efficiency is not important (when is THAT the case?) then Router A can individually announce all eight routes. To reduce the size of routing updates and improve efficiency, Router A can announce all the routes with a single announcement. Let’s examine this in binary, or as I like to say, let’s pay attention to the man behind the curtain. Here is what is happening in the second octet in binary:
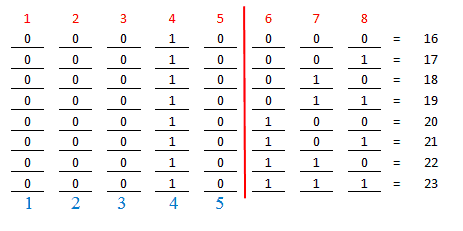
As we examine the binary numbers from left to right, our goal is to note at what point the numbers start changing. Notice they are all the same in column one. The same goes for columns two, three, four, and five. But in column six, the first four numbers are zeros and the second group of four is all ones. So if we imagine we have a slider bar and we slide it to the right until the numbers start changing, we will end up with a chart like this:
So the original Net IDs all had sixteen bit subnet masks. If we keep in mind that the first eight are all 172, and therefore do not change, then we realize the supernetting occurs in octet two. Counting the first octet as eight bits, then we start counting in octet two, just the bits that do not change. Notice I have labeled the first five bits of octet two as unchanged. So take the first eight, add the next five, and the result is thirteen bits that don’t change for this summary announcement.
Now to determine what the summary announcement will be. The best place to begin a summary announcement is on a nice binary block number. In our example, the first Net ID has a second octet value of sixteen, which is one of the powers of two, and thus a nice binary block number. Let’s write our summary:
172.16.0.0 /13
The mask is as we have calculated it at thirteen bits. So Router A can efficiently announce all the routes behind him in a single announcement, as shown above.
If this seems confusing, a cool way for it to make more sense is to imagine that the summary announcement is a subnetting problem. Let’s say we are a junior network admin and the big cheese gave us a piece of paper with ONLY this information on it: 172.16.0.0 /13. Can we determine where our piece of this network starts and ends? If we examine the mask, we see that it moves five bits into octet two. Five bits into the subnet mask field give us a subnet mask value in decimal of 248. From our previous discussions, we can determine that a subnet mask value of 248 gives us a network increment of eight. The value of octet two, sixteen, is a multiple of eight, so that is our starting network ID. If we are incrementing by eight, that means the next section of network starts at 16 + 8, or 24. So our piece, what the boss gave us on a piece of paper, must end just below 172.24.0.0. So our highest number just below that would be 172.23.255.255. So the last subnet ID of a network with a sixteen bit mask would be 172.23.0.0 /16. This means our section of the networks range from 172.16.0.0 to 172.23.0.0, which is exactly what the summary announcement is supposed to convey.
If it seems tedious to list out all the Net IDs in binary, never fear, there is a faster way. I do recommend doing it the long way the first few times so it all makes sense. Once you feel comfortable with what summary announcements do, try this shortcut. If you count the number of networks to be announced in the above example, you get a total of eight. How many bits in binary do you need to represent eight numbers (counting from zero to seven)? You need three bits. If you roll three bits through all their possible positions, you can represent all the decimal numbers from zero to seven. That means those three bits (in the second octet) will be changing. If three of the eight are changing, that means the other five (8 – 3) are not. So eight unchanging bits in octet one, plus five unchanging bits in octet two gives you thirteen unchanging bits, which is the same answer we obtained using the long method.
Give this a shot and see how you do. It’s quite fun actually – like solving a mystery!
Until next time, supernet like a superhero!!
Mark Jacob
Cisco Instructor – Interface Technical Training
Phoenix, AZ
You May Also Like
Cisco subnet, IPv4, Net ID, octet binary, Subnet, subnet mask, subnetting, Supernetting
A Simple Introduction to Cisco CML2
0 3914 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 649 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 752 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments