Creating a Custom RBAC Role with the Lync Server Management Shell
Creating a Custom RBAC Role with the Lync Server Management Shell
Lync 2010 comes with several pre-defined RBAC roles. The thing is, they’re all globally scoped. For example, if I add your account to the CSUserAdministrator USG in Active Directory, you now have the ability to modify, disable, or move users (to name a few) anywhere in the organization. Let’s take a look at a few ways you can customize this.
User Scopes
First, let’s say that we have a globally dispersed topology, and administrators in the respective regions should only be able to manage the users in the same location. What we would want to do is create a custom role based off of the existing CSUserAdministrator. We would then scope this role to a specific OU, such as the “North America” OU, where the users are located.
The first thing you need to do is come up with a name for your custom RBAC role. In this case, we’ll use NA_Lync_Admins. Next, you’ll need to create a new Active Directory Universal Security Group named NA_Lync_Admins. Finally, fire up the Lync Management Shell and use the New-CSAdminRole cmdlet to create your custom role:
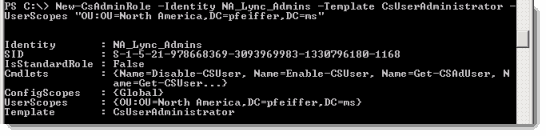
Notice that in this example, the distinguished name for the North America OU is used, and prefixed with the tag “OU:”. This is the piece that creates a user based scope connected to that OU. Anyone added to the NA_Lync_Admins group in AD will be able to manage users in that location in AD.
Server Scopes
Now, in our geographically dispersed deployment, we also need to control modifications to server settings. This is where config scopes come into play. For example, the CSServerAdministrator provides admins with the ability to modify settings on specific servers. Since we have locations all over the globe, our Lync topology probably has several sites. We can use these site definitions to act as a configuration scope for our custom role.
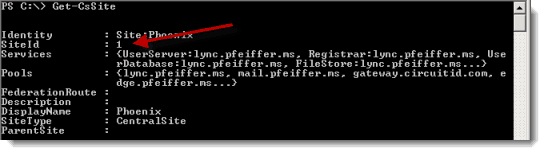
Just as before, we’ll create a new Active Directory Universal Security Group for each regional group of server administrators. This time, we’ll create one called Phx_Lync_Server_Admins for our site in Phoenix. First, we need to run Get-CSSite to determine the site id:
Next, we can use the New-CSAdminRole cmdlet to create the custom role:
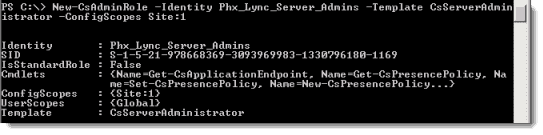
Again, its important that the custom role match the name of our group in AD. Also, notice that this time we’ve used the -ConfigScopes parameter to define the site scope. Ensure that, just as above, you’ve used the “site:” tag, followed by the site id for that particular site. Just as before, when an administrator is added to the Phx_Lync_Server_Admins, he’ll be able to make configuration changes on servers that are only part of that site in the Lync topology.
Enjoy!
Mike Pfeiffer – Microsoft MVP
Director of Unified Communications
Interface Technical Training
You May Also Like
A Simple Introduction to Cisco CML2
0 3901 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 645 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 731 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments




See what people are saying...