In this blog we will explore how to demote a domain controller in Windows Server 2012 Active Directory Domain Services (AD DS).
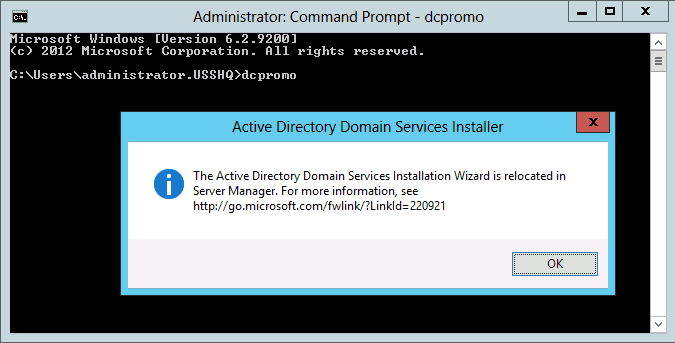
In previous versions of Windows Server to demote a domain controller you would use the DCPROMO.exe utility. In Windows Sever 2012 the DCPROMO utility has been deprecated.
In Windows Server 2012 we will use Server Manager or PowerShell to demote the DC. In this blog I will be using the GUI to demote the server manager. So let’s get started.
To demote a DC from AD DS complete the following steps:
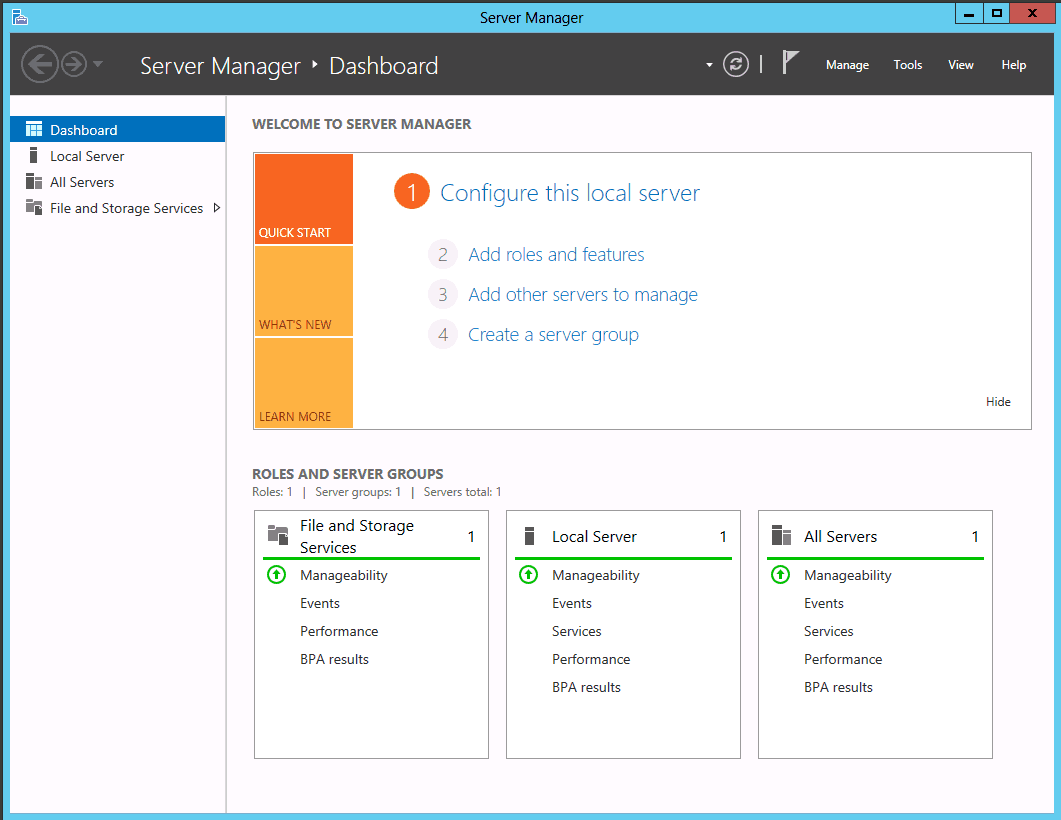
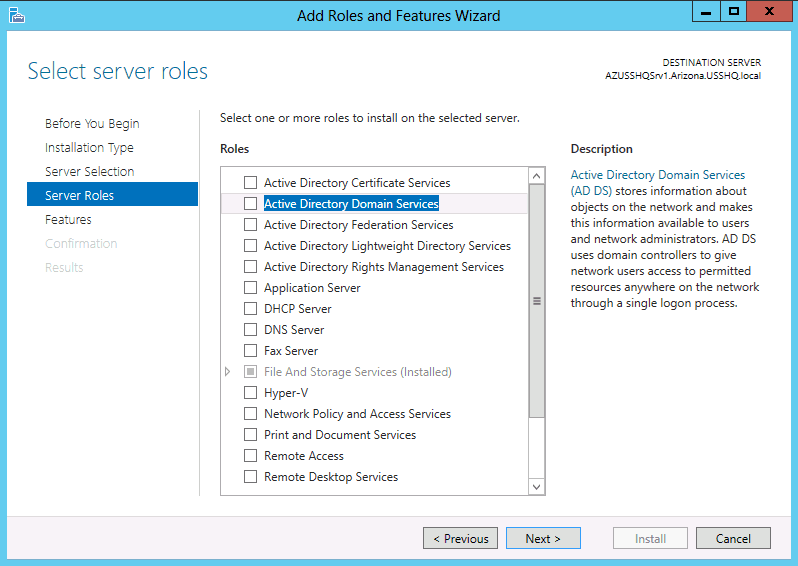
Use Server Manager to remove the Active Directory Domain Services Role.
Launch Server Manager, select the Manage drop down menu, select Remove roles and features.
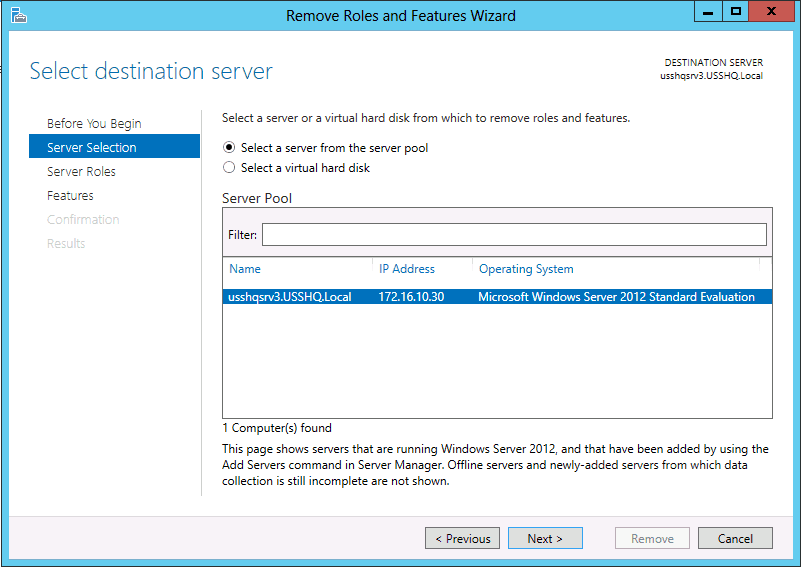
- Review the Before You Begin page, Click Next.
- On the Select installation type page ensure Role-based or feature-based installation radial button is selected, click Next.
- On the Select destination server page Select the desired server from the Server Pool.
Note: The 2012 Server Manager allows roles and features to be installed remotely.
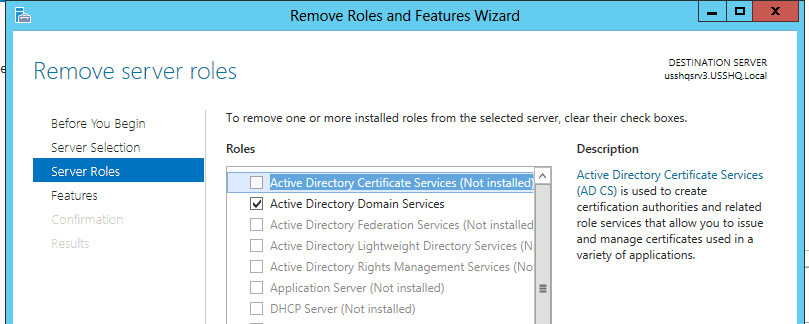
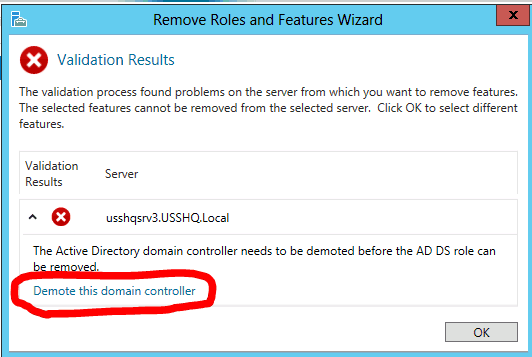
- On the Remove Roles and Features Wizard, click on the Active Directory Domain Services box to remove the check box.
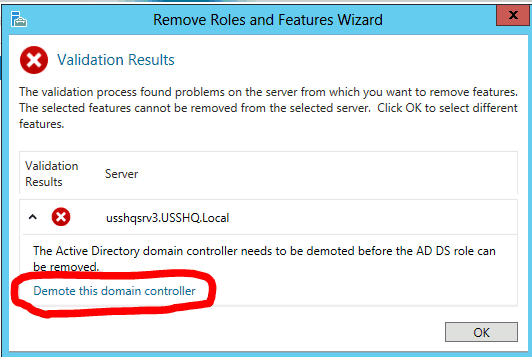
- The Remove Roles and Features dialog box Remove features that require Active Directory Domain Service pops up, select Remove Features.
- On the Remove Roles and Features Wizard dialog box Validation Results box will appear. The domain controller must be demoted before continuing. Click on Demote this domain controller.
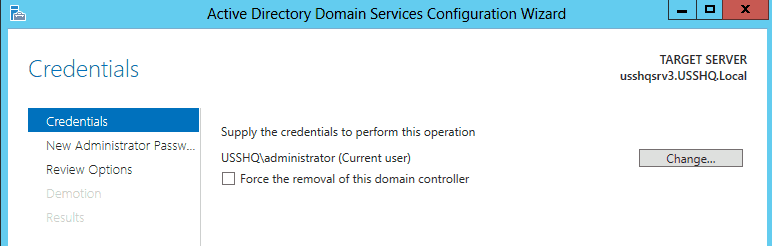
- On the Active Directory Domain Services Configuration Wizard enter the required credentials to demote this server, click Next.
Note: To demote replica domain controller you must be at the least a Domain Admin to remove an entire domain from the forest or to demote the last DC of a Forest you must provide Enterprise Admin credentials.
Note: Only select Force the removal of this domain controller if the DC and not communicate with the remaining DCs.
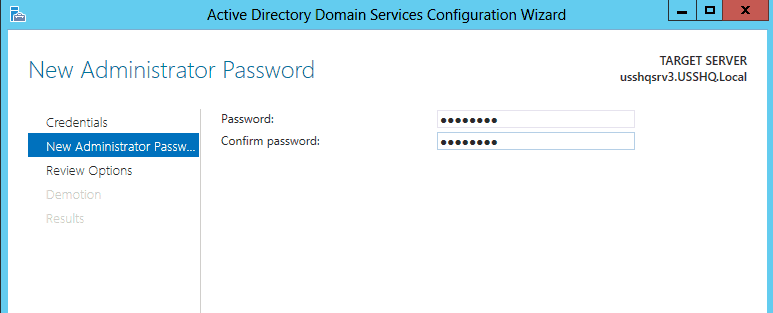
- On the New Administrator Password, enter and confirm the new local administrator account password, click Next.
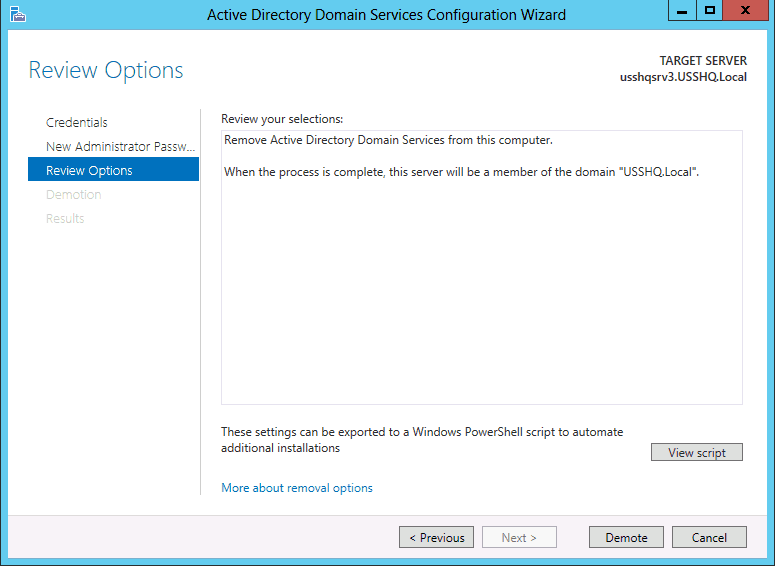
- On the Review Options verify the information is correct and click Demote.
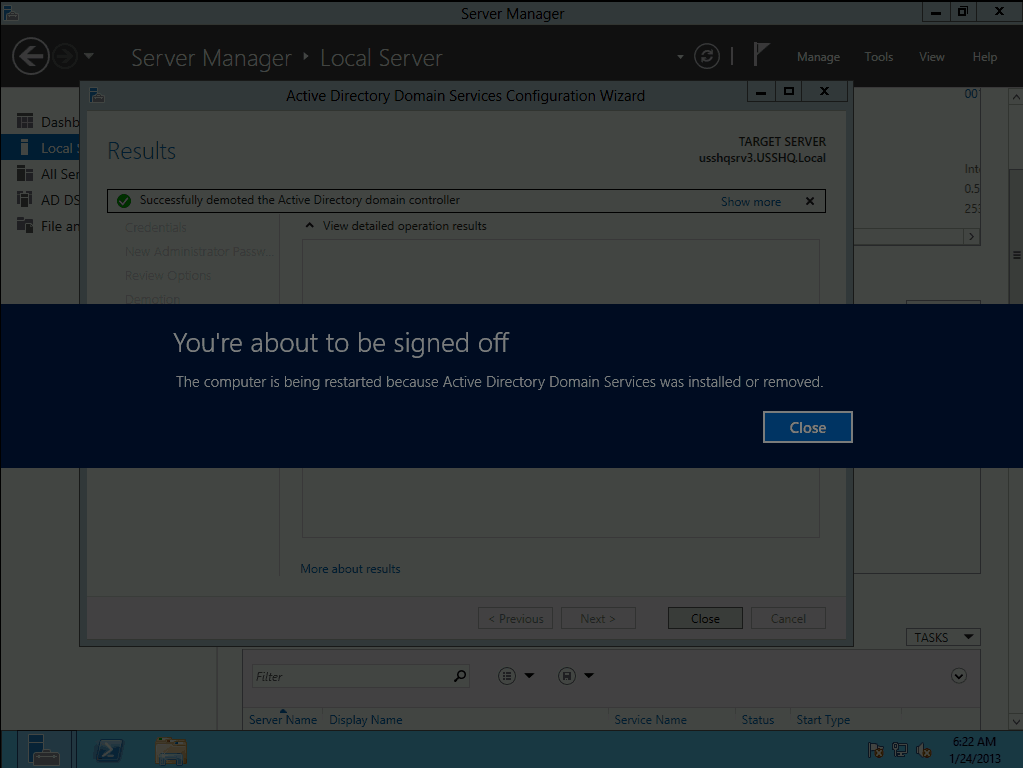
This will begin the demotion process. To finish the demotion the server will automatically restart.
Note: When the server restarts it will be a member of the domain that is was previously a domain controller in.
Note: The Binaries for AD DS are still installed on the server. If this server is not going to be promoted back to a domain controller in the future rerun the Remove Roles and Features Wizard to remove the AD DS Role from the server.
Verifying the Removal of AD DS
- Logon to the server hosting the DNS service for the domain using the Administrator account credentials.
- Launch the DNS console and verify the deletion of Service Records for the removed domain controller.
Active Directory Domain Services is now been removed from this server.
Until then, RIDE SAFE!
Rick Trader
Windows Server Instructor – Interface Technical Training