An introduction to GLBP in Cisco IOS
An introduction to GLBP in Cisco IOS
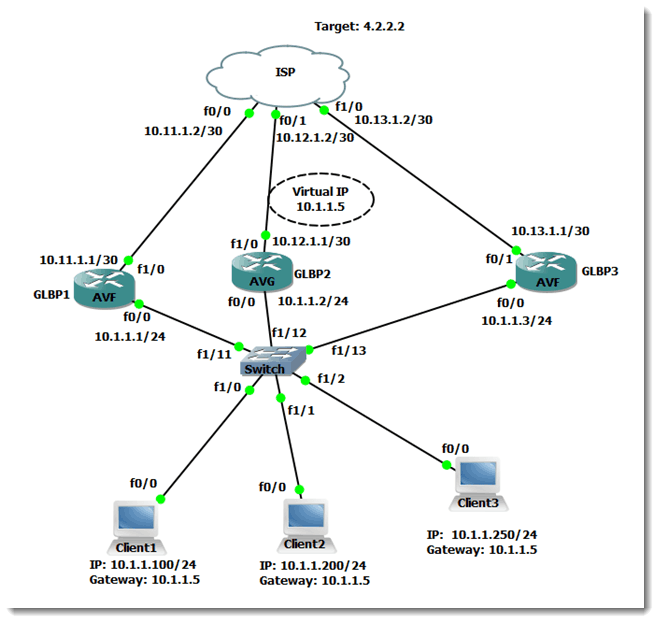
I have posted blogs dealing with HSRP and VRRP. Today’s topic takes this idea a step beyond what is possible with those protocols by introducing the concept of Gateway Load Balancing Protocol (GLBP). Let’s begin by viewing the network scenario I used for this blog:
Figure 1
GLBP is a Cisco proprietary protocol which was made available in 2005. It is designed to be an improvement over the existing FHRPs – HSRP and VRRP – because it allows full utilization of router resources without having to create multiple groups, which is a limitation of HSRP and VRRP. GLBP has the following functions: Active Virtual Gateway (AVG) and Active Virtual Forwarder (AVF). In a GLBP group, the members elect one of the routers to be the AVG. The AVG assigns virtual MAC addresses to each member of the GLBP group. If the AVG dies, one of the other members of the group will take over this functionality.
An AVF is a gateway which assumes to role of forwarding packets that are sent to the virtual MAC address which is assigned to that AVF by the AVG. GLBP then load balances among all the gateways that are active in this GLBP group using one of three load-balancing mechanisms. The mechanisms are weighted load-balancing, host-dependent load-balancing, and round-robin load-balancing-which is the default. In weighted load-balancing, a forwarding router is assigned load based upon the weight that it advertises. In host-dependent load-balancing, an individual host will always use the same virtual MAC address as long as that MAC address is active in the GLBP group. In round-robin load-balancing, an AVG responds to client ARP requests with the MAC address of the next available router (AVF) in the group, similar to a dealer dealing cards.
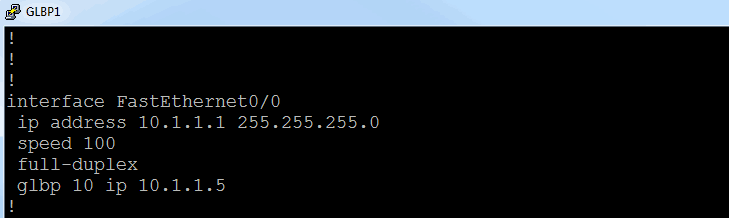
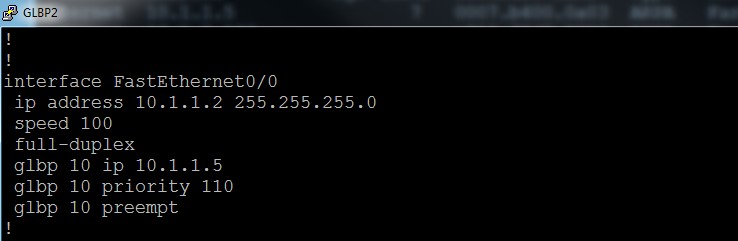
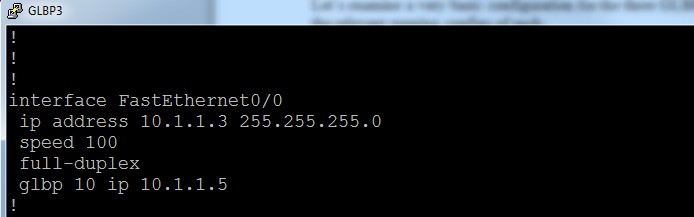
Let’s examine a very basic configuration for the three GLBP routers shown in Figure 1. Here are the relevant running configs of each:
Figure 2
Figure 3
Figure 4
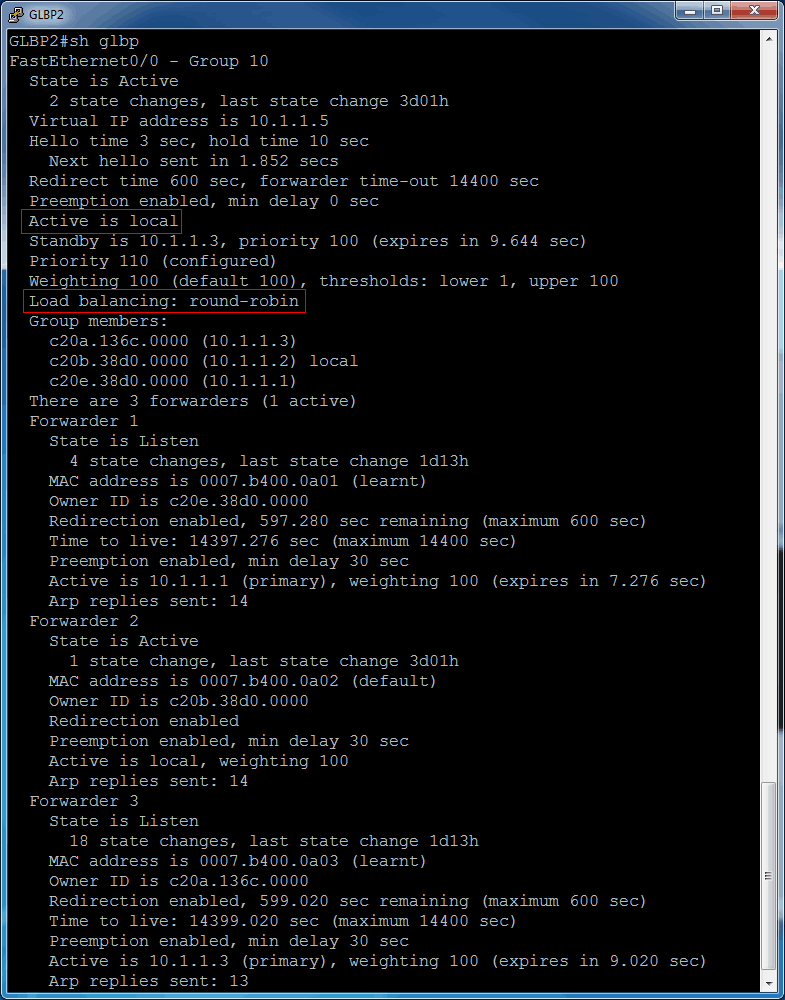
As shown in Figure 1, I want GLBP2 to win the role of AVG. To make this happen, I used the priority command on GLBP2, which is displayed in Figure 3. The default priority value is 100, so by setting GLBP2 to a higher value, it becomes the AVG. With the configurations shown, note the output of show glbp on glbp2:
Figure 5
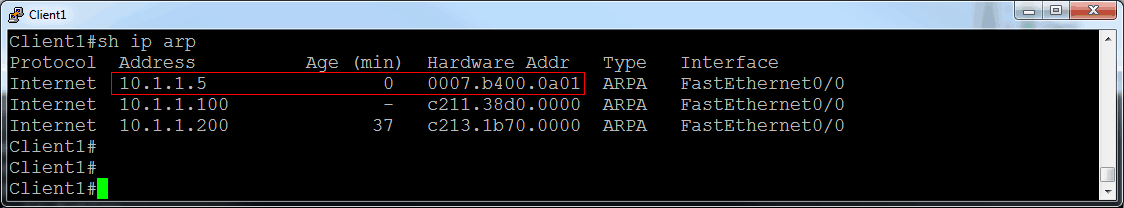
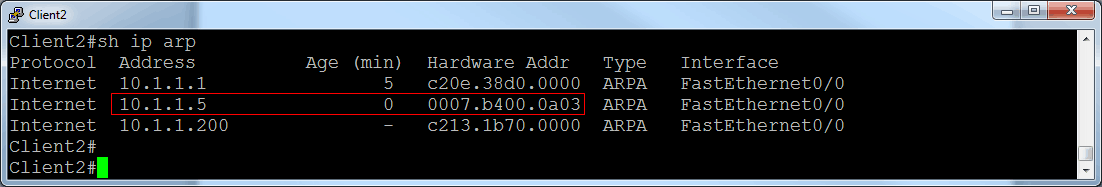
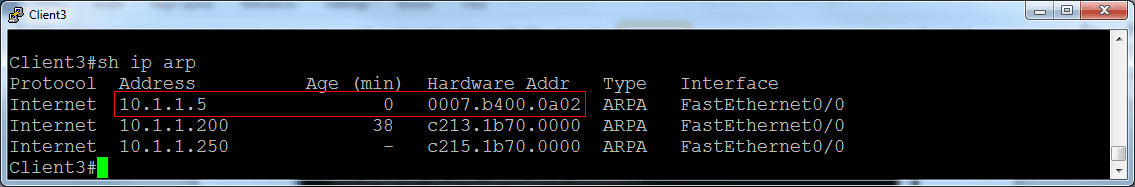
All three clients are configured with a default gateway IP address of 10.1.1.5, which also happens to be the virtual IP address configured in GLBP. Now that the entire network is up and running, let’s examine the ARP information on each of our clients. I have issued the ping 10.1.1.5 command on each client and received replies. Take a look at what each client has learned:
Figure 6
Figure 7
Figure 8
As you can see, each client has an entry for the IP address of its default gateway of 10.1.1.5. However, each client has a different MAC address stored for that IP address. This is the result of the round-robin load balancing that is happening behind the scenes. Also noteworthy is the fact that the AVG also participates in the forwarding of packets. It does not just sit around and delegate the user load to the AVF routers.
There is much more involved in fine-tuning GLBP in your network. In this blog I just wanted to hit the very basics of initial configuration. In future blogs I will explore how GLBP can track upstream destinations and adjust itself accordingly. I hope you will tune in and enjoy those discussions as well.
Until next time…
Mark Jacob
Cisco Instructor – Interface Technical Training
Phoenix, AZ
You May Also Like
AVF, Gateway Load Balancing Protocol, Gateway redundancy, GLBP, HSRP, Virtual MAC address, VRRP
A Simple Introduction to Cisco CML2
0 3901 0Mark Jacob, Cisco Instructor, presents an introduction to Cisco Modeling Labs 2.0 or CML2.0, an upgrade to Cisco’s VIRL Personal Edition. Mark demonstrates Terminal Emulator access to console, as well as console access from within the CML2.0 product. Hello, I’m Mark Jacob, a Cisco Instructor and Network Instructor at Interface Technical Training. I’ve been using … Continue reading A Simple Introduction to Cisco CML2
Creating Dynamic DNS in Network Environments
0 645 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader teaches how to create Dynamic DNS zones in Network Environments. Video Transcription: Now that we’ve installed DNS, we’ve created our DNS zones, the next step is now, how do we produce those … Continue reading Creating Dynamic DNS in Network Environments
Cable Testers and How to Use them in Network Environments
0 731 1This content is from our CompTIA Network + Video Certification Training Course. Start training today! In this video, CompTIA Network + instructor Rick Trader demonstrates how to use cable testers in network environments. Let’s look at some tools that we can use to test our different cables in our environment. Cable Testers Properly Wired Connectivity … Continue reading Cable Testers and How to Use them in Network Environments



See what people are saying...